Secrets Hub
AWS Secrets Manager(ASM), Azure Key Vault(AKV), Google Secret Manager(GSM)에서 비밀 정보에 대한 중앙 집중식 관리, 가시성 및 순환을 제공하며 HashiCorp Vault에 대해서는 검색 기능을 제공합니다.
보관된 비밀 정보가 어디에 있는지 알고 계신가요?
이 간단한 자가 평가를 통해 숨겨진 저장소 확산을 발견하고, 위험을 파악하며, 비밀 정보 스캔 준비 상태를 확인하십시오.
클라우드 애플리케이션 보안 강화
개발자가 기존 워크플로우를 계속 사용해 내장형(네이티브) 저장소에 있는 비밀 정보에 접근할 수 있도록 하면서도 보안 팀에 가시성과 CyberArk의 중앙 집중식 비밀 관리의 모든 이점을 제공합니다.
클라우드 공급자의 내장형 저장소를 사용하여 앱을 구축하고 배포하는 보안, 개발자 및 클라우드 운영 팀의 요구 사항을 충족하기 위해 지금 시작하십시오.
중앙 집중식 관리 및 순환
보안 팀에 비밀 정보에 대한 가시성, 제어 및 순환 기능을 제공하면서 통합 정책을 시행하십시오.
개발자 경험 유지
개발자가 지금처럼 클라우드 공급자의 네이티브 비밀 정보 저장소를 계속 사용할 수 있도록 합니다.
완벽한 검색 기능
저장소에 있는 관리형/비관리형 비밀 정보를 검색하고 관련 인사이트를 제공합니다.
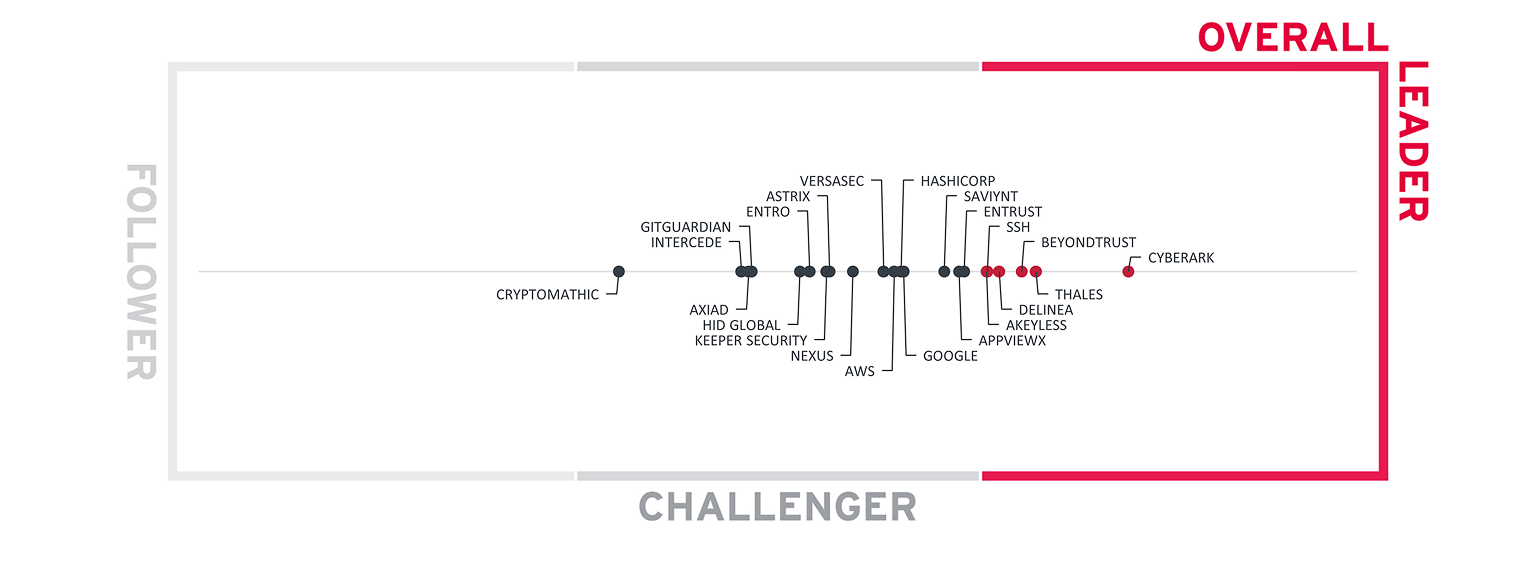
CyberArk, 2025년 KuppingerCole Analysts Leadership Compass에서 엔터프라이즈 비밀 정보 관리 부문 종합 리더로 선정
개발자의 경험을 변경하지 않고 클라우드 네이티브 저장소에서 비밀 정보를 중앙에서 관리하고 검색하십시오.
개발자 워크플로우에 영향을 주지 않으면서 중앙 집중식 비밀 정보 관리의 모든 이점을 누리십시오.
중앙 집중식 관리 및 순환
기존 보안 프로세스와 인프라를 활용하여 중앙 집중식 통제를 구축하고 비밀 정보에 대한 통합 순환 및 기타 정책을 시행하십시오.
개발자 및 운영 경험 유지
개발자는 AWS Secrets Manager, Azure Key Vault, Google Secret Manager를 계속 사용하여 비밀 정보에 접근할 수 있으며, 보안 팀은 중앙 집중식 가시성을 확보할 수 있습니다. Secrets Hub를 통해 보안 팀은 중앙 거버넌스 외부에서 생성 및 관리되는 HashiCorp Vault 사용 현황도 검색할 수 있습니다.
검색 및 가시성
AWS, Azure, GCP 네이티브 저장소 전반에 걸쳐 비밀 정보에 대한 통찰력을 확보하고, 중앙 보안 감독 범위 밖에서 개발자나 팀이 관리할 수 있는 HashiCorp Vault 인스턴스를 발견하십시오.
확장 가능하고 포괄적
CyberArk의 Identity Security Platform에 통합되어 모든 애플리케이션 유형, 인간 및 머신 아이덴티티에 대한 비밀 정보를 중앙에서 안전하게 보호하고 관리할 수 있습니다.
SaaS의 단순성
운영 및 배포를 간소화하고, 높은 수준의 확장성과 가용성을 제공하면서 전문 기술의 필요성을 최소화합니다.
AWS, Azure 및 GCP 환경 전반에 걸쳐 저장소 확산을 제거하고 중앙 거버넌스 외부에서 운영되는 HashiCorp Vault 사용에 대한 가시성을 확보하십시오.


“(with) identity security and especially PAM, CyberArk is the key service DZ BANK uses to protect our IT infrastructure. Since integrating CyberArk into our environment, privilege management and security have definitely improved. Fundamentally, it always comes back to having control over privileges and being able to manage secrets.”
Kurt Sand, GM,
Machine Identity Security at CyberArk

개발자의 기존 환경에 맞춰 애플리케이션 보안 개선
다양한 유형의 비인간 아이덴티티를 보호하기 위한 주요 고려 사항
클라우드, 하이브리드 환경 등을 아우르는 비밀 정보의 중앙 집중식 보안을 간소화하는 방법을 살펴보십시오.
관련 리소스 살펴보기
데모 요청
검색 및 가시성: AWS, Azure, GCP 전반의 비밀 정보를 확인하고 중앙 보안 감독 범위 외부에 있는 HashiCorp Vault 인스턴스를 발견하십시오.
중앙 집중식 관리 및 순환: AWS, Azure, GCP 네이티브 저장소 전반에서 일관되게 비밀 정보를 관리하고 순환하십시오.
개발자 경험 유지: AWS, Azure, GCP 및 HashiCorp Vault를 사용해 개발자 워크플로우를 유지하면서 중앙 집중식 가시성을 추가하십시오.
저장소 확산 방지: 모든 주요 클라우드 공급자의 네이티브 비밀 정보 저장소와 HashiCorp Vault에 걸쳐 비밀 정보를 중앙 집중식으로 관리하여 운영을 간소화하고 가시성을 높이십시오.




