Asegure cada identidad, humana y de máquina, con el nivel adecuado de controles de privilegios.

Proteja las identidades.
Bloquee a los atacantes.
Proteja a la perfección las identidades a lo largo del ciclo de acceso a cualquier recurso en cualquier infraestructura, incluidos los sistemas híbridos, SaaS y multinube. La plataforma de Seguridad de la Identidad de CyberArk es la primera línea de defensa contra ciberdelincuentes y accesos no autorizados para proteger lo que más importa.
Acceso seguro y fluido para todas las identidades
Al combinar un SSO seguro, una MFA adaptativa, la gestión del ciclo de vida, los servicios de directorio y el análisis del comportamiento de los usuarios, le ayudamos a agilizar las operaciones y a ofrecer a los usuarios un acceso sencillo y seguro a los recursos (locales, en la nube o híbridos) desde cualquier lugar y con cualquier dispositivo.
Controles inteligentes de privilegios
Aplique controles inteligentes de privilegios de primera clase en toda la infraestructura de TI, así como controles específicos para proteger las necesidades exclusivas de los usuarios, proveedores externos, endpoints e identidades de máquina cuando acceden a datos confidenciales.
Automatización y orquestación flexibles de la identidad
Agilice los procesos de RR. HH., garantice que los usuarios tengan el acceso adecuado a los recursos adecuados, permita la conformidad con las normativas sectoriales o gubernamentales y mejore la eficiencia en todos los ámbitos con la orquestación y la gestión del ciclo de vida, permisos y derechos, y servicios de directorio y federación.
Definición de seguridad de la identidad
Centrada en los controles inteligentes de privilegios, la seguridad de la identidad protege a la perfección el acceso para todas las identidades y automatiza de forma flexible el ciclo de vida de la identidad con la detección y prevención continuas de amenazas, todo ello con un enfoque unificado.
Aplique controles inteligentes de privilegios en todo el ciclo de vida de la identidad
Amplíe los controles inteligentes de privilegios diseñados para el usuario con más privilegios, como un administrador, a una gama más amplia de identidades humanas y de máquina, siempre que se requiera un acceso permanente o just-in-time.
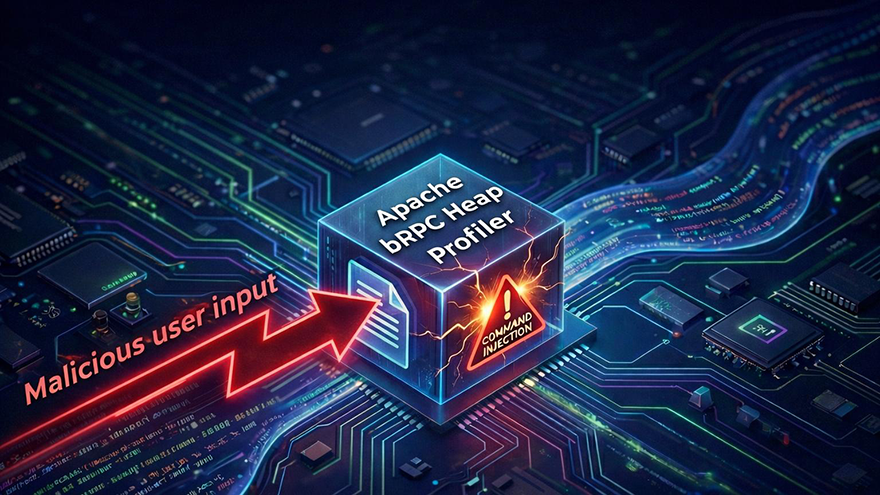
Investigación e innovación en materia de amenazas: CyberArk Labs
Un equipo de investigadores dedicado a examinar las nuevas técnicas de ataque para que las organizaciones de todo el mundo puedan reforzar su postura de seguridad.
“Si podemos controlar la identidad, podemos detener la mayoría de los ataques modernos. Esto es lo que yo llamo un auténtico enfoque Zero Trust y por eso utilizamos CyberArk. Es lo que me ayuda a dormir tranquilo”.
Brian Miller, CISO, HealthFirst