Proteggere ogni identità – umana e macchina – con il corretto livello di controlli dei privilegi.

Proteggere le identità.
Bloccare gli attaccanti.
Proteggere le identità senza soluzione di continuità durante l’intero ciclo di accesso a ogni risorsa, in qualsiasi infrastruttura, comprese quelle ibride, SaaS e multi-cloud. CyberArk Identity Security Platform è la prima linea di difesa contro attori malintenzionati e accessi non autorizzati per proteggere ciò che conta di più.
Accesso sicuro e senza soluzione di continuità per tutte le identità
Combinando SSO sicuro, MFA adattiva, Lifecycle Management, Directory Services e di User Behavior Analytics, ti aiutiamo a semplificare le operazioni e fornire agli utenti accesso semplice e sicuro alle risorse – on-premise, cloud o ibride – da ogni luogo, su qualsiasi dispositivo.
Controlli intelligenti dei privilegi
Applicazione di controlli intelligenti dei privilegi di livello assoluto sull’intero patrimonio IT, nonché di controlli differenziati per proteggere le esigenze specifiche di forza lavoro, fornitori di terze parti, endpoint e identità delle macchine che accedono ai dati sensibili.
Automazione e orchestrazione flessibili dell’identità
Semplificare i processi HR, assicurare che gli utenti abbiano il giusto accesso alle risorse corrette, consentire conformità alle normative di settore o governative e migliorare l’efficienza in tutti i settori con l’orchestrazione e la gestione del ciclo di vita, permessi e abilitazioni, servizi directory e di federazione.
L’Identity security richiede un approccio olistico incentrato sui privilegi
Grazie ai controlli intelligenti sui privilegi, Identity security protegge fluidamente le identità umane e macchina che accedono ad applicazioni, infrastrutture e dati, e automatizza con flessibilità il ciclo di vita delle identità, il tutto con un approccio unificato. Identity Security consente l’approccio Zero Trust grazie all’applicazione del privilegio minimo con continuità di rilevamento e protezione dalle minacce alle identità.
Applicazione di controlli intelligenti dei privilegi nell’intero ciclo di vita dell’identità
Estendere i controlli intelligenti dei privilegi sviluppati per l’utente con più privilegi, come l’amministratore, a una gamma più ampia di identità umane e macchine, ogni volta in cui viene richiesto un accesso permanente o Just-in-Time.
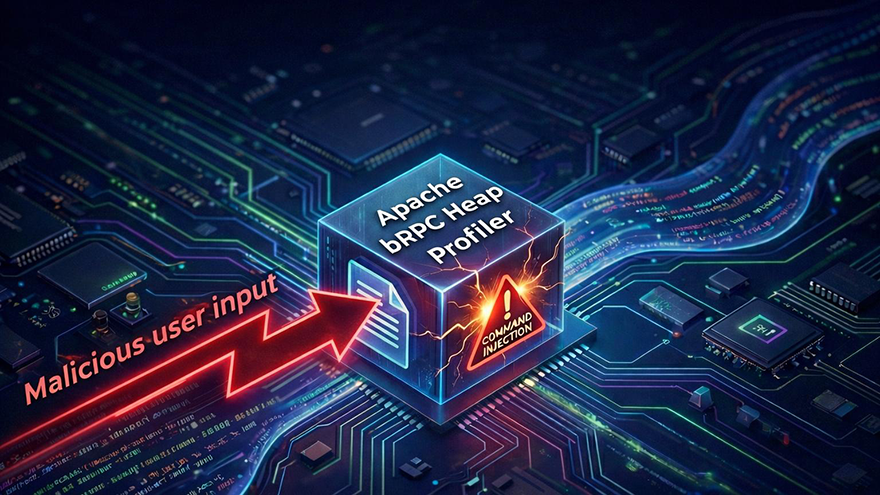
Analisi delle minacce e innovazione: i CyberArk Labs
Un team di ricercatori impegnato ad analizzare le tecniche di attacco emergenti, per supportare le aziende di tutto il mondo a rafforzare la propria postura di sicurezza.
“Se possiamo controllare l’identità, siamo in grado di fermare la maggior parte degli attacchi moderni. Questo è ciò che io definisco il vero Zero Trust ed è il motivo per cui ci affidiamo a CyberArk. Ed è questo che mi aiuta a dormire sonni tranquilli.”
Brian Miller, CISO, HealthFirst