CyberArk Endpoint Privilege Manager vs Broadcom Carbon Black App Control
Proactive Endpoint Protection – Stop Attacks Before They Execute
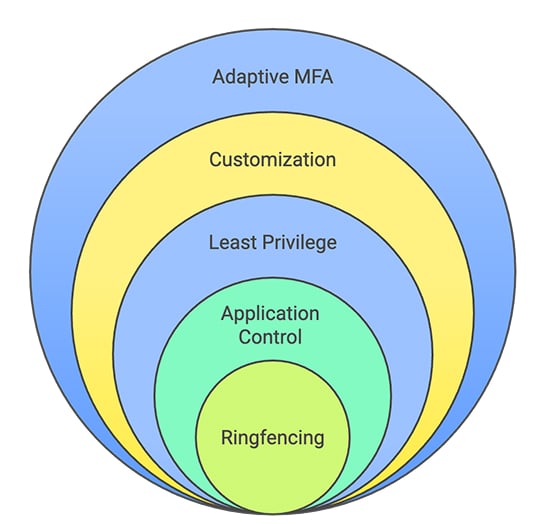
CyberArk Endpoint Privilege Manager (EPM) proactively secures endpoints by enforcing least privilege and adaptive application controls. CyberArk EPM leverages intelligent allowlisting, denylisting, greylisting, and advanced ringfencing. This approach shrinks the endpoint attack surface, prevents ransomware and reduces operational overhead.

Enforce least privilege to secure your endpoints. CyberArk Endpoint Privilege Manager combines advanced application control with robust privilege management.





1
Privilege Management vs. Application Whitelisting Focus
CyberArk Endpoint Privilege Manager (EPM) is designed to enforce the principle of least privilege by enabling organizations to remove local admin rights from endpoints while still allowing users to perform necessary tasks through granular privilege elevation. This includes support for just-in-time and policy-based elevation of applications, scripts, and commands based on context.
In contrast, Carbon Black App Control is primarily focused on application whitelisting and lockdown, restricting which applications can run on endpoints through predefined allowlists. It does not offer native, dynamic privilege elevation, making it less flexible in supporting user productivity without compromising security.
The Takeaway
CyberArk EPM offers dynamic, context-aware privilege elevation, while Carbon Black App Control is more rigid and centered around application execution control.
“CyberArk Endpoint Privilege Manager gave us the visibility and granular control needed to implement both least privilege and ‘default deny’ application control with minimal disruption to the organization.”
Ken Brown, Chief Information Security Officer
Milliken & Company
2
Adaptive Endpoint Protection Powered by Identity-Aware Controls
CyberArk EPM provides multi-layered threat protection with identity-aware controls and least privilege enforcement, blocking attackers even when they’re exploiting legitimate tools or privileges. CyberArk’s approach blends identity security with endpoint controls: it can “block and contain attacks at the endpoint” by combining least privilege enforcement, Threat Intelligence and Behavioral Analytics, and granular application control.
In contrast, Carbon Black takes a reactive stance, detecting threats during or after execution. It lacks identity awareness, leaving systems open to misuse on legitimate apps. As a result, gaps are left open and attacks may begin causing damage before being stopped.
The Takeaway
CyberArk EPM stops threats before they start; Carbon Black reacts after damage.
3
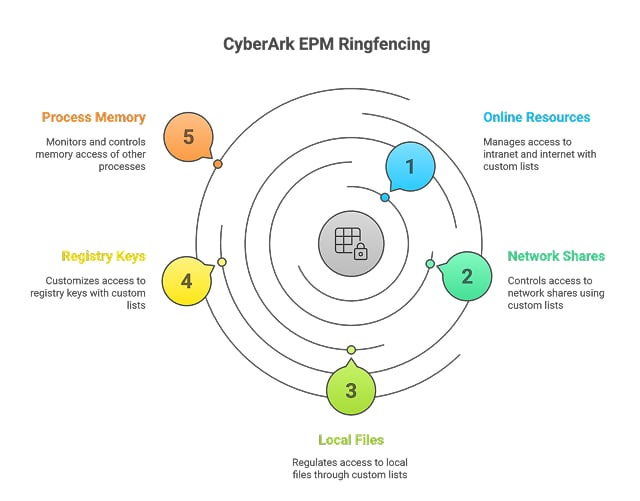
Advanced Application Ringfencing Tailored to Your Organization
CyberArk offers advanced ringfencing controls that can be applied globally to greylisted apps or tailored to specific policies. By containing unknown applications instead of outright blocking them, EPM limits risk while preserving productivity. Visibility into user behavior and app usage can help inform smarter policy decisions and reduce administration overhead.
Carbon Black Application Control is rigid in design and lacks ringfencing capabilities to contain apps without outright blocking. This forces security and IT teams to constantly review and manually approve apps, delaying access and hampering productivity.
The Takeaway
CyberArk’s flexible ringfencing enables secure containment without disruption. Carbon Black App Control’s rigid model lacks this agility and increases the operational burden on security and IT teams.
Protect every endpoint. Give attackers nowhere to hide.
Explore how CyberArk Endpoint Privilege Manager helps your organization stop threats before they start, reduce operational burden, and strengthen endpoint security.
Enforce least privilege and block risky applications without disrupting user productivity.