防禦攻擊
防範資料外洩的主要原因 — 身分和憑據遭竊取
防止攻击
確保身分安全,保護最重要的資產
少了實體邊界,網路漏洞防不勝防,但我們可以避免遭受損失。採用以特權為中心的做法保護身分的公司能夠更周全地保護自己免受各種類型的攻擊。
防止攻击
超半數的財星 500 大企業信任 CyberArk 隔離威脅及保護他們最關鍵的資產和資源。
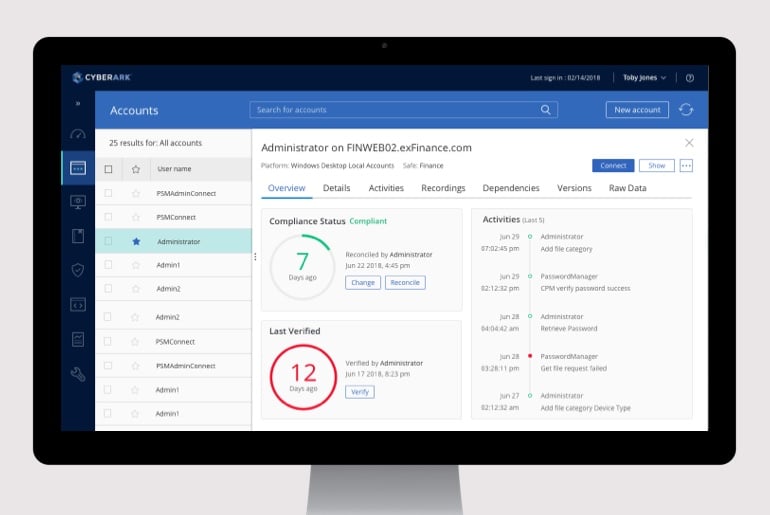
特權存取管理器
透過管理帳戶、憑據和連線及修復風險活動,隔離威脅並防止特權遭竊取。
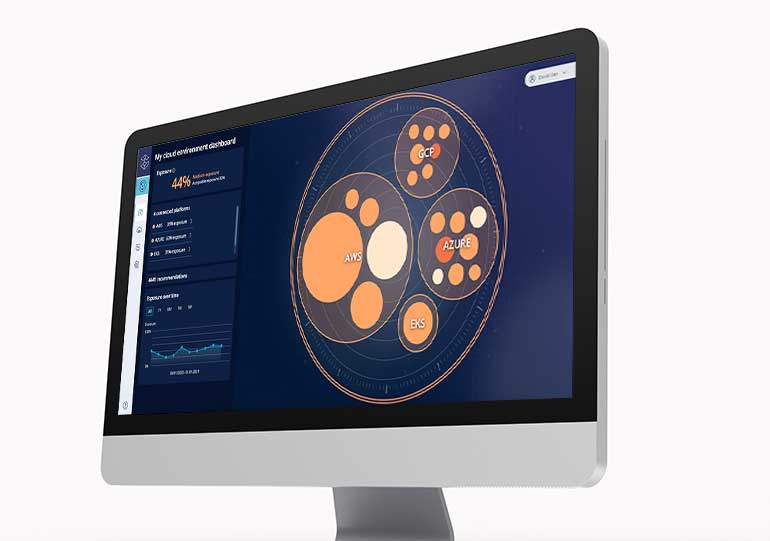
雲端權利管理器
修復未使用及錯誤配置的權限,以主動防禦內部及外部威脅。
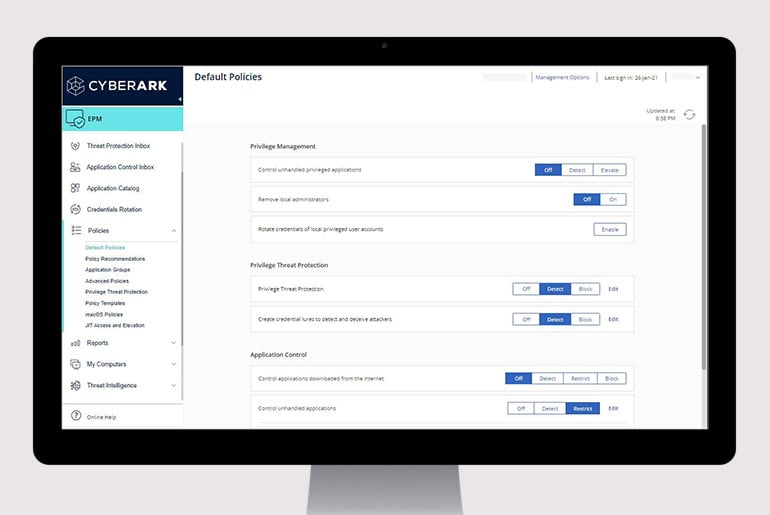
端點裝置特權管理器
實施最低權限、控制應用程式並防止 Windows 和 Mac 電腦和 Windows 伺服器上的憑據竊取以遏止攻擊。
多因素驗證
利用由 AI 驅動的強大風險感知式無密碼方法驗證身分。


供應商特權存取管理器
透過智慧型手機執行雲端生物識別身分驗證,確保遠端供應商安全地連接至您的組織。
身分安全基礎知識

身分安全:為什麼很重要,為什麼現在就需要
安全為先,生產效率並重
全方位的安全防護
以下是幾個我們能協助您在數位世界中無畏前行的方法。
了解
相关
资源
申请演示
預防資料外洩的最大主因
保護您最關鍵的業務資產
與特權存取業界公認的領導者合作