Privileged Access
Sicherheitsverstöße sind unvermeidlich. Schäden schon.

Least Privilege durchsetzen
Least-Privilege-Sicherheitskontrollen anwenden. Schützen Sie privilegierten Zugriff über alle Identitäten, Infrastrukturen und Apps hinweg, vom Endgerät bis zur Cloud.
Gegen Angriffe verteidigen
Schutz vor den Hauptursachen von Sicherheitsverletzungen – kompromittierte Identitäten und Anmeldedaten.
Digitales Business ermöglichen
Digitale Erlebnisse bieten, die Sicherheit und Reibungslosigkeit in Einklang bringen.
Audit und Compliance sicherstellen
Eine einheitliche Lösung für identitätsorientierte Audit- und Compliance-Anforderungen.
Angreifer schon im Ansatz stoppen
CyberArk Privileged Access Management Lösungen decken eine breite Palette von Anwendungsfällen ab, um privilegierte Anmeldedaten und Secrets zu sichern, wo auch immer sie vorhanden sind: On-Premise, in der Cloud und überall dazwischen.
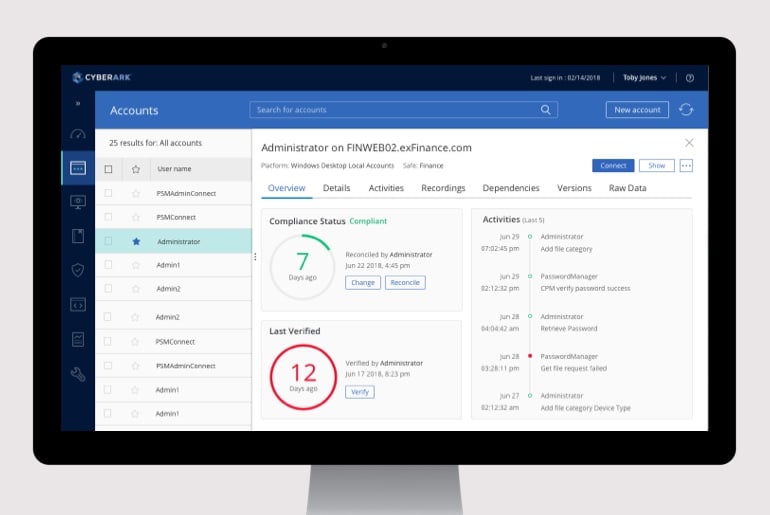
Privileged Access Manager
Erkennen und verwalten Sie kontinuierlich privilegierte Konten und Anmeldedaten, erfassen und überwachen Sie privilegierte Sitzungen und beheben Sie riskante Aktivitäten in allen Umgebungen.
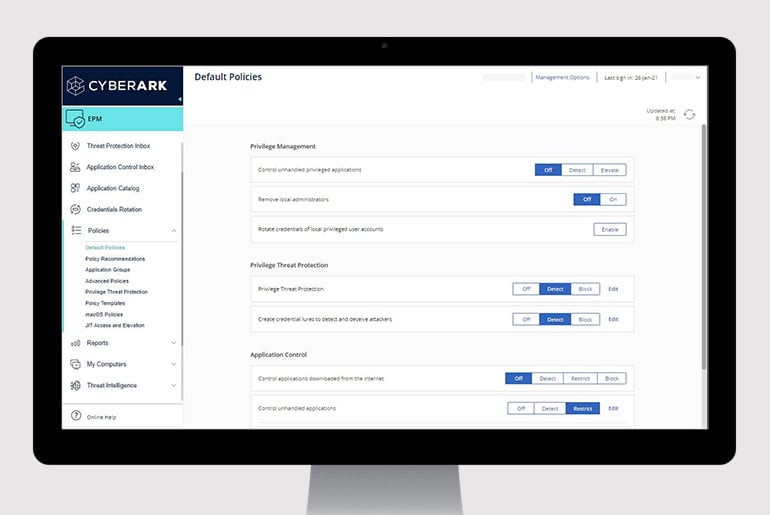
Endpoint Privilege Manager
Setzen Sie Least Privilege durch, kontrollieren Sie Anwendungen und verhindern Sie den Diebstahl von Anmeldedaten an Windows- und Mac-Desktops sowie Windows-Servern, um Angriffe einzudämmen.

Vendor Privileged Access Manager
Anbietern einen sicheren Remote Access auf die sensibelsten IT-Assets ermöglichen, die von CyberArk verwaltet werden, ohne dass VPNs, Agenten oder Passwörter erforderlich sind.
Sicherer Cloud-Zugriff
Sicherer nativer Zugriff auf jede Ebene einer Multi-Cloud-Umgebung, der Just-in-Time mit Zero Standing Privileges bereitgestellt wird.

CyberArk Marketplace
Durchsuchen Sie unseren Online-Marketplace, um Integrationen zu finden.
Marketplace besuchen
















Rundum sicher
Hier sind nur einige weitere Möglichkeiten, wie wir Ihnen helfen können, in einer digitalen Welt furchtlos voranzukommen.
Betriebliche Effizienz steigern
Die Komplexität und Belastung der IT reduzieren und gleichzeitig den Schutz des Unternehmens verbessern.
Ihre verteilte Belegschaft schützen
Ermöglichen Sie Nutzern den Zugriff auf jedes Gerät, überall und zur richtigen Zeit.
Ransomware stoppen
Verhindern Sie laterale Bewegungen mit 100%igem Erfolg gegen mehr als 3 Millionen Formen von Ransomware.
Sichere DevOps und Cloud
Sicherer Zugriff für Maschinenidentitäten innerhalb der DevOps-Pipeline.
Identity security: identitäten absichern
mit intelligenten Zugriffskontrollen

2025 Gartner® Magic Quadrant™ für Privileged Access Managament
Verwandte Ressourcen erkunden
Eine Demo anfordern
Privilegierte Konten und Anmeldedaten verwalten
Least Privilege am Endpoint durchsetzen
Übermäßige Cloud-Berechtigungen entfernen
Sicheren Remote Access von Lieferanten ermöglichen
CyberArk Has Patent Rights Relating To This Technology – https://www.cyberark.com/patents