Secure the Future of Privileged Access
Secure access for every identity – human, machine, and AI – across any infrastructure.
The Identity Security Challenge: Uncontrolled Privilege
87% of organizations have experienced at least two successful identity-centric breaches in the past 12 months.
Eliminate Standing
Privileges
Static credentials are open doors. Zero standing privileges shuts them.
Secure Access in Dynamic Environments
Organizations adopt multi-cloud, Kubernetes, and AI-first technologies, requiring access to be fast and fluid.
Balance Speed and Security
Developers and engineers need secure, seamless access that won’t impede velocity.
Key Features Required to Prevent Identity Attacks
Unified Privileged Access Everywhere
One platform to Secure any identity – human, machine or AI – to any target, on-prem or cloud.
Trusted PAM Controls
Combine vaulting, rotation, and session controls with Just-in-Time access and Zero Standing Privileges.
Smart Audit and Response
Detect, respond, and govern privileged activity in real-time – automatically.
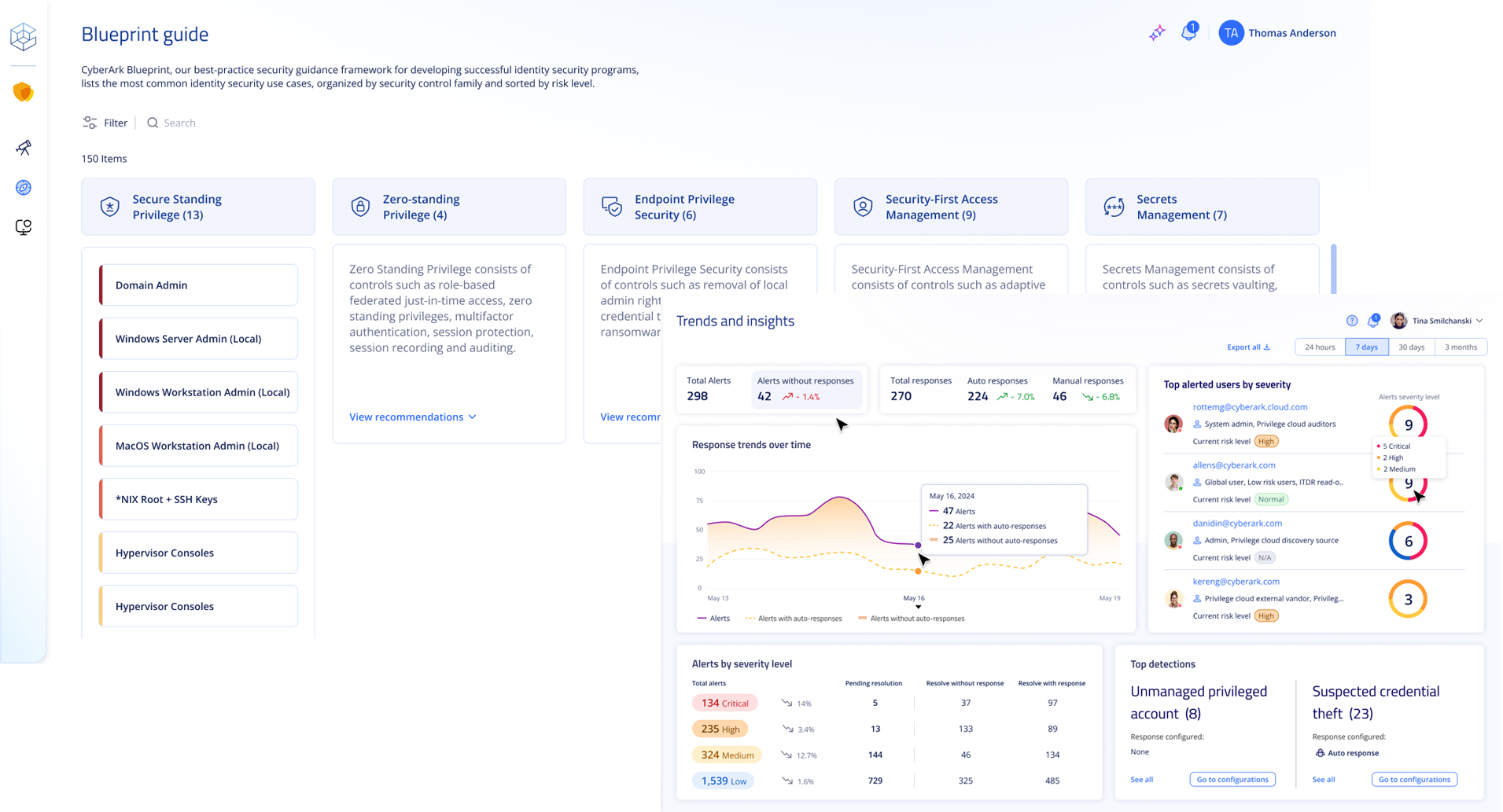
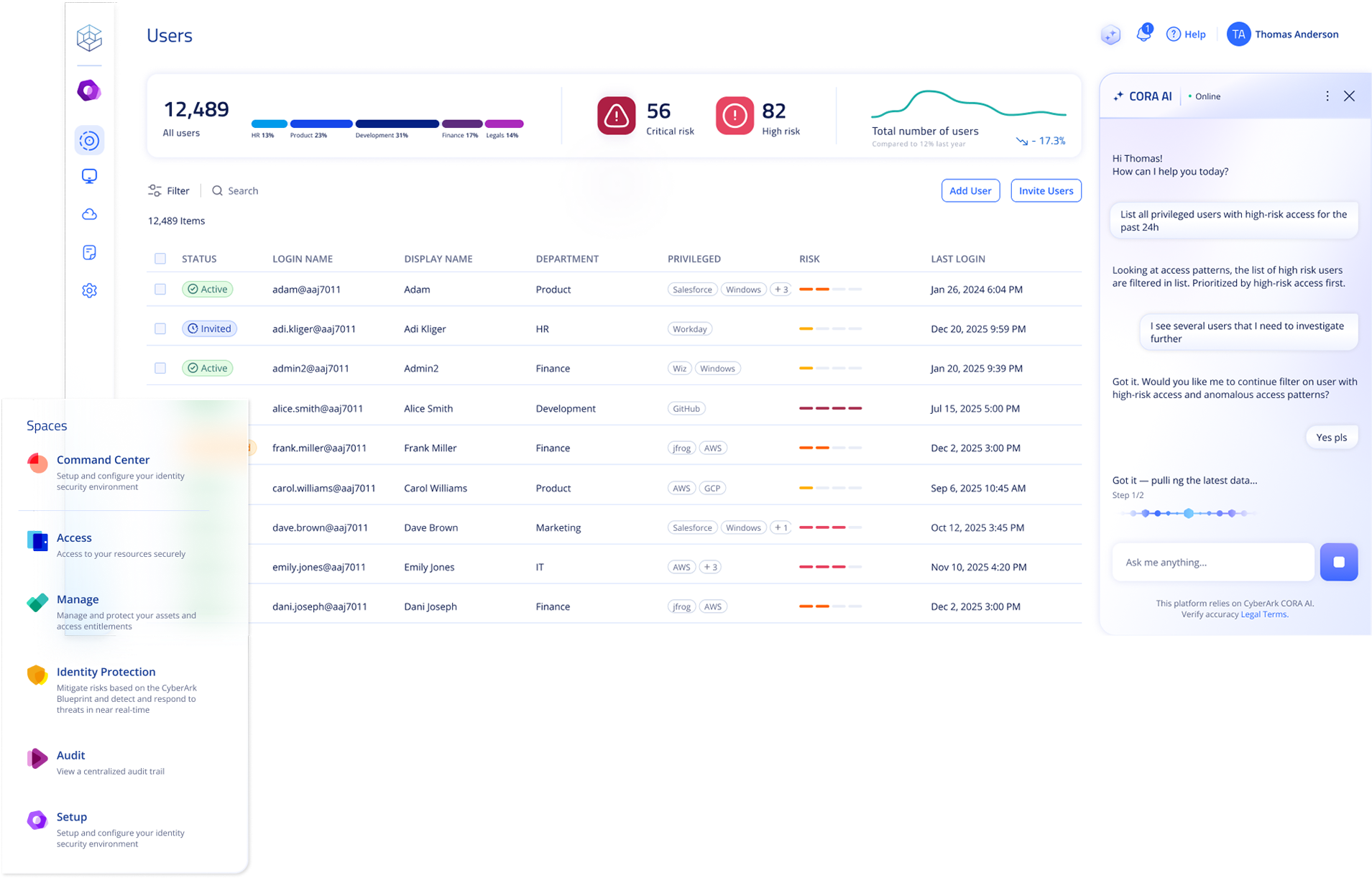
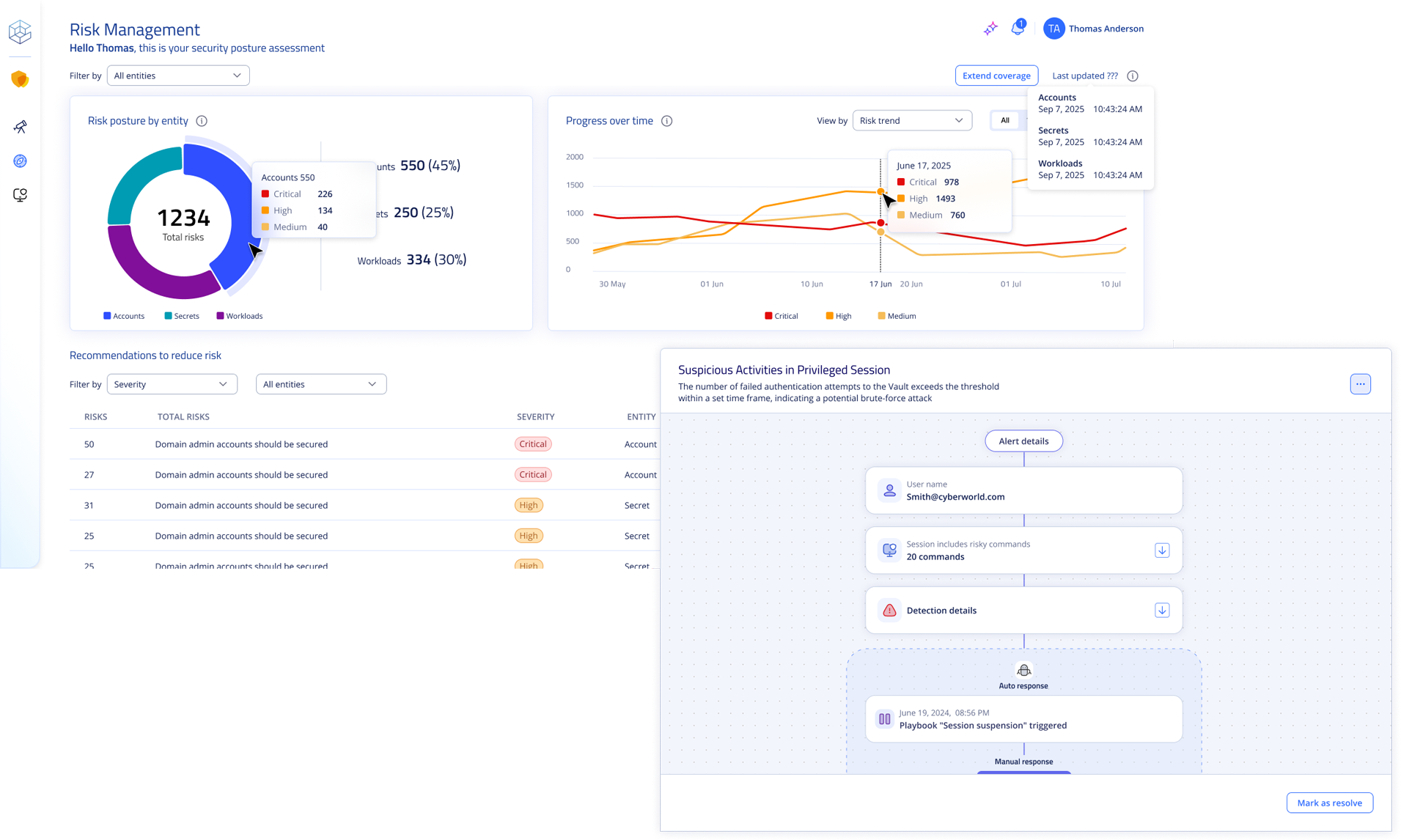
See it in Action: The CyberArk Identity Security Platform

Discover and Eliminate Hidden Privilege Risks
Continuously detect unmanaged credentials, excessive entitlements, and orphaned access. Stay audit-ready automatically.

Protect Against Identity-Based Attacks
Apply Just-in-Time access and enforce Zero Standing Privileges across humans, machines, and AI identities with ephemeral creds and controlled sessions.

Measure and Prove Risk Reduction
Monitor access behavior, validate policy effectiveness, and visualize privilege reduction over time.
Built to stay ahead.
Don’t take our word for it – see why analysts call CyberArk a leader.
Schedule a personalized demo
- Eliminate standing privileges.
- Streamline audit and compliance.
- Empower your teams with secure, seamless access.
















