Conjur Secrets Manager Enterprise
A self-hosted solution to secure secrets for cloud-native, containerized applications, CI/CD pipelines and DevOps tools.
Conjur Secrets Manager Enterprise
Keep your secrets safe
Secure credentials used by applications, scripts and other non-human identities with CyberArk’s secrets management software.
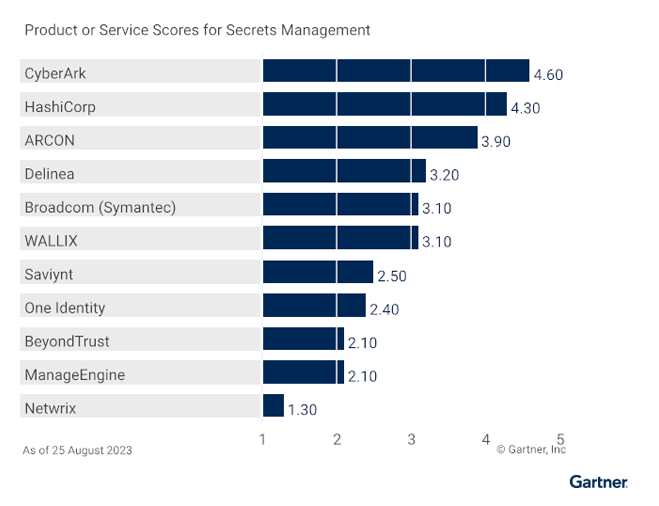
The highest score for Secrets Management use case in the 2023 Gartner® Critical Capabilities for PAM
Explore why CyberArk was ranked highest for the Secrets Management use case.
Secure credentials with confidence
Enforce secrets management for applications, scripts and other non-human identities.
- Manage, rotate and monitor credentials used by apps
- Provide developers with tools to simplify securing apps
- Eliminate the pain of generating audit trails

Protect the enterprise. Secure application credentials.
Empower your applications – while keeping secrets out of attackers’ hands.
Comprehensive Secrets Management
Secure all credentials and secrets used by non-human users. Eliminate hard-coded credentials in applications. Rotate credentials based on policy.
Robust authorization and audit
Authenticate applications and containers using native application attributes and role-based access controls. Record key events with tamper-resistant audit.
Enterprise scale and availability
Meet stringent enterprise resiliency, scalability, and performance requirements with distributed, high-availability architecture.
Extensive integrations library
Accelerate deployment with validated integrations, including popular DevOps tools, CI/CD toolchains, automation tools, PaaS platforms and public cloud platforms.

Secure all your application secrets with Conjur
Discover how Conjur can help enterprises secure secrets across DevOps and CI/CD tools such as Ansible, Cloudbees CI and Jenkins; container orchestration platforms like Kubernetes; RPA tools such as UiPath; and mainframes that run high-volume, mission-critical apps.
Identity security centered on
intelligent privilege controls

CyberArk named a Leader in the 2023 Gartner® Magic Quadrant™ for Privileged Access Management – again.

"CyberArk has been the best vendor I have worked with in my 20+ year IT career. CyberArk delivers great products that lead the industry in managing privileged access."
IT Security Manager, Security and Risk Management

"With CyberArk, we are confident that we have implemented technology that will work with us as our business grows and develops."
Jean-Pierre Blanc, Bouygues Telecom

"This isn’t just a compliance check-box exercise, we’re actively designing and aligning policies to cybersecurity best practices to strengthen our overall security posture and align internal teams."
Joel Harris, Manager

"CyberArk gave us the visibility and granular control needed to implement both least privilege and ‘default deny’ application control with minimal disruption to the organization."
Ken Brown, CISO

"With RPA and Cloud migrations, credentials are becoming more and more spread out away from 'normal' controls. CyberArk can spread out to cover all of the scenarios in a standard way."
Information Security Consultant, Enterprise Cybersecurity Solutions Technologies
Identity security that knows you but doesn’t slow you
Explore all the ways CyberArk gives you peace of mind to move fearlessly forward.
Request a demo
Centrally manage all credentials
Safely automate processes while protecting the enterprise
Minimize the burden of audit and compliance
