Secure Cloud Access
Zero Standing Privileges secures identities at every layer of your multi-cloud environment – without impacting native cloud user experience.
Security Teams: Manage Identities Across your Cloud Estate
Help security teams protect cloud access and meet compliance requirements in a native, secure manner. Reduce risk with Zero Standing Privileges, increase efficiency with embedded workflows, and work effectively with granular access controls.

Centralized View
Become the center of cloud access with a single point of control for all cloud access.
Automated Approvals
Streamline manager approvals using existing tools and workflows to increase efficiency when granting elevated access requests.
Granular Controls
Provide each user with the appropriate level of access or create the relevant access request for the relevant approver using CyberArk’s market-leading control of Time, Entitlements, and Access (“TEA”).
Increased Adoption
Prevent the “this won’t work for me” argument by delivering a secure native access experience protected by the seamless integration of Zero Standing Privileges into existing workflows.

Download the Secure Cloud Access Data Sheet
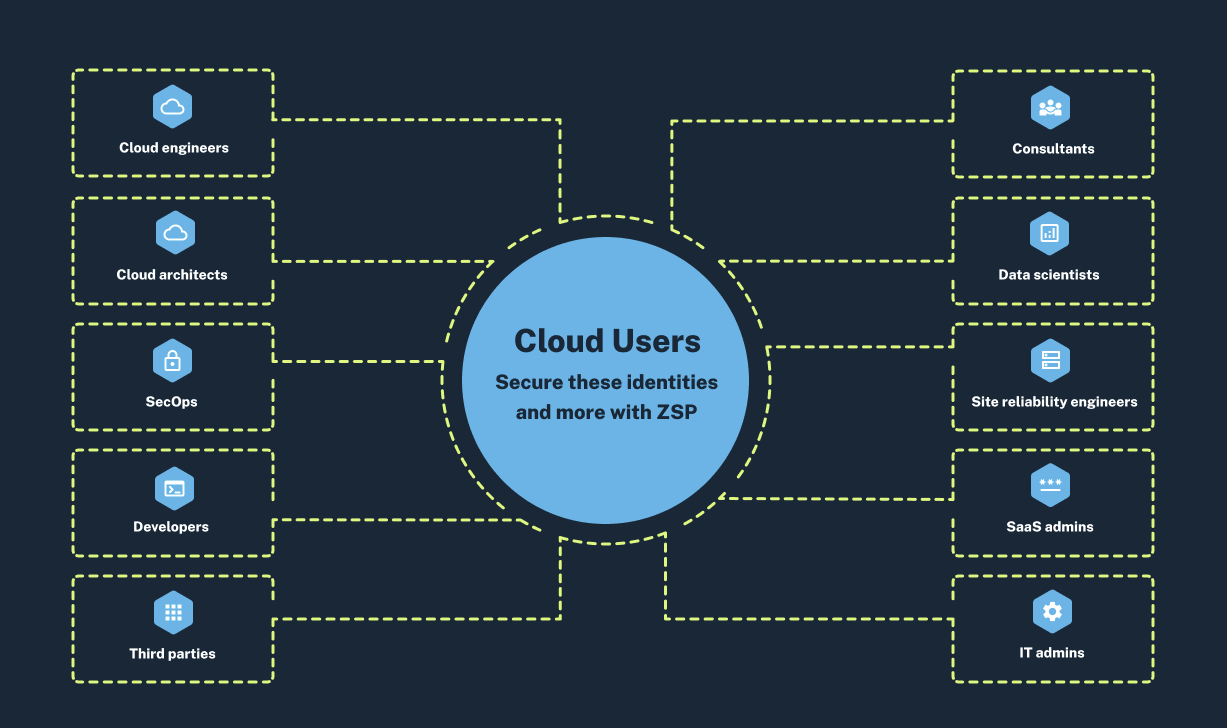
Secure Cloud Access provides users like developers, SRE’s, SaaS admins, and more with secure, native access to the cloud via console or CLI. Learn how Zero Standing Privileges scales to reduce the risk of excess entitlements.
Holistic Control and Robust Security for Cloud Access
Improve your security team’s ease of management for cloud identities – without compromising security. Explore how CyberArk does it best in our 30-day free self-serve trial.
Apply Zero Standing Privileges
Remove all standing permissions. Grant entitlements just-in-time.
Reduced attack surface
Grant entitlements just-in-time
Provision native access quickly and securely


Define Access Policies Globally
Define how users access cloud consoles by setting up centralized secure policies. Manage entitlements with a holistic view that reduces complexity and increases control.
Enable Dynamic Break-Glass Access
Empower engineers, developers, SRE’s and other cloud users to securely request and rapidly receive the access they need to respond to critical situations (“crit-sit”). This nimble process results in measurable cyber risk-reduction.

Integrate Seamlessly
Integrate capabilities into existing service desk or ChatOps tooling to efficiently handle access requests.
Streamline approvals with our no-code automation solution
Accelerate speed of approvals while increasing flexibility
Automate approvals and apply risk-based rules to reduce the number of tasks at hand
Seamless Experience for Cloud Users
Implement Zero Standing Privileges in your multi-cloud estate without disrupting productivity. Developers, cloud engineers, third party consultants, SaaS administrators, and many other users need to move quickly across cloud environments – from AWS to Azure to GCP. Facilitate innovation for agile cloud users while ensuring the security of their identities and your cloud infrastructure.
Native UX and Access to the Cloud
No agents, no hurdles. Deliver secure access to multi-cloud consoles with native user experiences.
Empower Cloud Users to Move Quickly
Give innovators the tools they need to request on-demand privileges and receive access quickly to support developmental velocity and productivity.
Innovation Across Multi-Cloud Environments
Scale Zero Standing Privileges across AWS, Azure, and GCP environments without friction to help cloud users securely navigate back and forth with ease.
Try CyberArk SCA MCP Server – Now Available in AWS Marketplace
Empower developers and AI agents to securely access cloud infrastructure right from your IDE, without embedded secrets or manual approvals.
Dynamic Access Controls
Zero Standing Privileges (ZSP) expands on Just-in-Time (JIT) to elevate access to cloud resources. Automate workflows and reduce the risk of standing access.
Native & Fast
Works directly with tools like Q Developer and Claude. No context switching. No security trade-offs.
Related
Resources
Learn how CyberArk can help you secure
your cloud without impacting productivity