CyberArk vs Teleport PAM
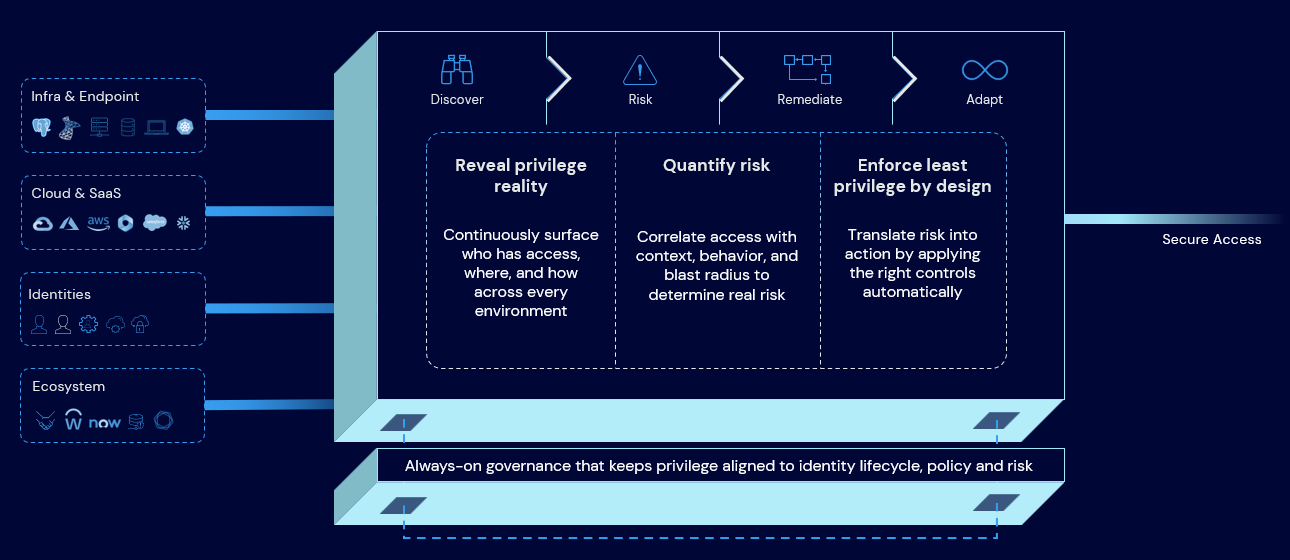
Identity Security Platform vs Infrastructure-Only PAM
Modern engineering and security teams want access that’s fast for builders, safe for the business, and practical across real infrastructure. Teleport and CyberArk both help reduce reliance on long‑lived credentials, but they differ in what they optimize for. Teleport focuses on making infrastructure access ephemeral. CyberArk focuses on making privilege exposure disappear over time, across identities and environments.
Because the real question is: what happens when privilege outlives intent?

Why Choose CyberArk
CyberArk
CyberArk is built to reduce privileged risk that persists outside sessions, across workforce, IT, developers, and machines. It enables continuous privilege control before, during, and after access.
Teleport
Teleport helps teams connect to cloud-native infrastructure using short‑lived credentials and session controls. The platform is designed for Linux/Kubernetes-centric teams with a heavy CLI and GitOps culture.
1
A Complete Identity Security Platform, Not Just Access
CyberArk is not just a point tool for infrastructure access: we deliver an Identity Security Platform to control privilege everywhere. Along with privileged session management, CyberArk provides secrets and certificate lifecycle management, endpoint privilege management, and identity access management, governance & administration (IDP & IGA). Manage your entire lifecycle of privileged access across human, machine, and AI agent identities, all with one vendor.
Teleport primarily focuses on infrastructure access and session controls. Teleport does not include a builtin enterprise secrets vault to store and rotate breakglass credentials, application secrets, or longlived API keys, so teams typically pair it with separate tools for secrets lifecycle management and broader identity risk reduction. This can increase tooling overhead as privileged access programs expand.
2
3
4
5
Broad Integrations with Enterprise Tools & DevOps Ecosystems
CyberArk integrates with a vast range of technologies (350+ certified integrations) – including SIEM/SOAR, ITSM ticketing, cloud IAM, CI/CD pipelines, directories and more — giving teams a consistent way to embed privileged access into automation, approvals, and monitoring workflows. These out-of-the-box integrations reduce custom development and align engineering and security processes.
Teleport provides APIs and an expanding integration ecosystem, but many connectors require additional configuration or community maintenance. Common enterprise workflows such as change-management approvals or SIEM log normalization may require scripting or third-party plugins. CyberArk’s C3 Technical Alliance minimizes deployment friction and supports your evolving environment.
















CyberArk vs Teleport: Critical Capability Comparison
Use this lens for every row: Does it reduce standing privilege over time, or only control access in the moment?
Teleport focuses on ephemeral access for infrastructure. CyberArk focuses on eliminating standing privilege across identities and environments with continuous control.
Comparison reflects publicly documented capabilities and common deployment patterns. Specific implementations vary by configuration and version.
Zero Standing Privilege / JIT Access
CyberArk
Dynamic ephemeral access across Windows and Linux with no persistent local accounts.
Teleport
Certificate-based ZSP for infrastructure. Windows access is supported but can require additional configuration. For local-user desktop provisioning, Teleport can create local Windows users on login and keeps them disabled rather than deleting them to preserve user profiles, which differs from “ephemeral user removed at session end” approaches.
Secrets Management & Credential Vaulting
CyberArk
Integrated secrets vault, automatic credential rotation, certificate lifecycle management, and machine identity security.
Teleport
Teleport has no built-in secrets manager or vault. It doesn’t manage static passwords or keys – it avoids them by using certificates for login. Any other secrets (database passwords, API tokens, etc.) must be stored and rotated using separate tools (e.g. AWS Secrets Manager or manual processes). This leaves a direct gap in managing your identity attack surface.
User Experience (UI/CLI/API)
CyberArk
Flexible UI, CLI, and API options for access; no OS modifications required on target systems (agentless for Windows).
Teleport
Strong CLI-first experience. Windows access requires installing a Teleport auth package, trusting Teleport’s CA, and adjusting RDP settings (e.g. disabling NLA) for certificate login.
Session Monitoring & Recording
CyberArk
Yes. Provides full session recording (video or keystroke logs for RDP/SSH) with a centralized audit trail. Security teams can search and replay sessions easily and integrate with SIEM/SOAR to automatically flag risky behaviors. CyberArk’s recordings and live monitoring help meet compliance and quickly investigate incidents.
Teleport
Yes. Teleport records and replays sessions (SSH, Kubernetes shell, and Windows desktop). Playback is available in the Web UI, with different recording formats. For advanced analytics and cross-system correlation, organizations often integrate Teleport audit events and recordings into SIEM/SOAR workflows.
Coverage Across Hosted, Legacy & Operational Technology
CyberArk
Yes. Works with both modern and legacy systems. CyberArk can broker access to databases, network devices, legacy servers, and Windows RDP sessions. An agentless approach allows connecting to systems that can’t run an agent (e.g. older OS or appliances). CyberArk can manage and rotate local admin passwords and still provide JIT access, critical for sensitive Windows/Unix deployments.
Teleport
Limited. Teleport is optimized for cloud native resources (Linux servers, Kubernetes, databases, and internal applications) and Windows desktops. Teleport supports agentless OpenSSH onboarding for some fleets, but it still requires SSH configuration changes and proxy reachability. Highly restricted legacy/OT environments where agents cannot be installed or OS/auth changes are prohibited may be difficult to onboard.
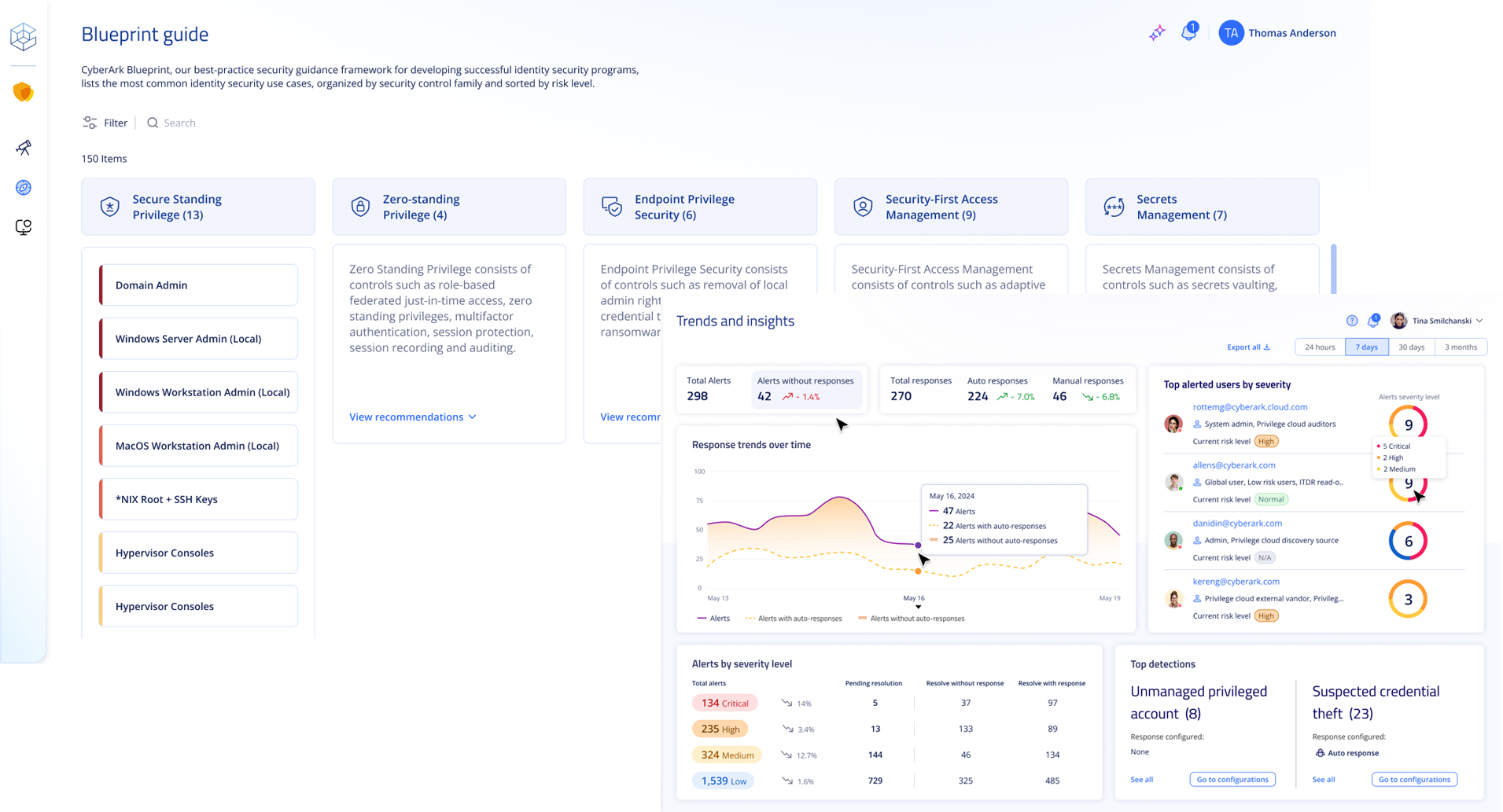
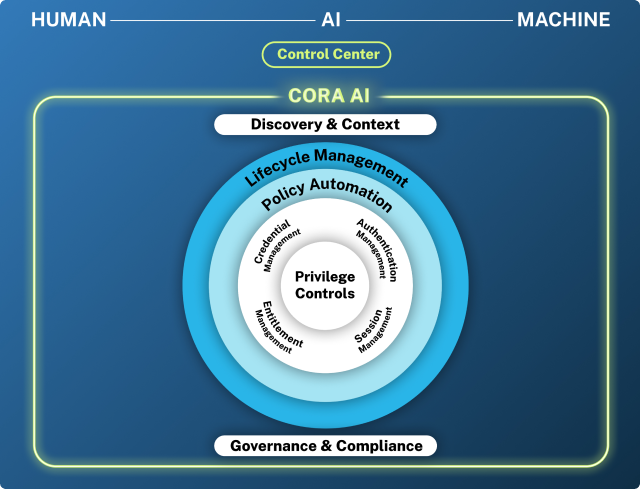
AI-Driven Security
CyberArk
Yes. Includes CORA™ AI, an AI assistant that helps admins work smarter – e.g. by automatically flagging unusual privileged activities, answering security queries in natural language, and providing remediation recommendations. This intelligent automation reduces manual steps and accelerates threat response.
Teleport
No. Broad identity security AI assistant. Teleport has emerging AI helpers (e.g. natural-language query over its Access Graph), but does not provide broad identity threat detection and response (ITDR) across workforce, apps, and non-Teleport systems.
Endpoint Privilege Management (Workstation/Server Endpoint Control)
CyberArk
Yes. Offers Endpoint Privilege Manager agents for Windows, Mac, and Linux to enforce least privilege on endpoints. This means even after connecting, users can be limited in what they can run, and on-demand privilege elevation can require justification or MFA. CyberArk EPM proactively blocks credential theft attempts and reduces the risk of ransomware and lateral movement.
Teleport
No. Teleport has no endpoint privilege control – it focuses only on access gateway functionality. Once a user is logged into a server via Teleport, Teleport cannot control their local actions or enforce least privilege on that machine. Organizations must rely on separate endpoint security tools to fill this gap.
Governance & Compliance
CyberArk
Yes. Provides Identity Governance and Administration (IGA) capabilities (via CyberArk Identity/”Zilla” engine) such as access reviews, automated provisioning/deprovisioning, separation-of-duties policies, and compliance reporting. CyberArk makes it easier to certify who has access to what and ensure that privileged access is compliant with policies and regulations.
Teleport
Teleport offers Access Lists and basic recertification for resources enrolled in Teleport, but it is not a full IGA solution. It does not manage joiner-mover-leaver workflows or access reviews across SaaS apps, business systems, or non-Teleport infrastructure.
Security Track Record
CyberArk
Enterprise-Hardened. CyberArk is extensively battle-tested in high-security environments (finance, government, etc.) and undergoes rigorous third-party assessments. Its closed-source architecture limits exposure, backed by a global support team and CyberArk Labs for threat research and platform security.
Teleport
Potential Concerns. Teleport is a legitimate remote access tool, but like many such tools, it has been used by threat actors as covert command-and-control (C2). Independent research has documented campaigns where Teleport was deployed this way.
Integrations & Ecosystem
CyberArk
Yes. 350+ pre-built integrations via the CyberArk Marketplace. Supports easy integration with enterprise directories (AD/LDAP), cloud IAM (AWS, Azure AD, GCP, etc.), ticketing systems, SIEM/SOAR, DevOps CI/CD pipelines, container platforms, and more – with minimal configuration. CyberArk’s platform is designed to fit into large organizations’ existing workflows and toolchains.
Teleport
Limited. Teleport offers APIs and plugins, but far fewer native integrations. The Teleport integration catalog is growing, yet many connectors are community-driven or require third-party tools. This can increase deployment effort and complexity.
Frequently Asked Questions
No. Teleport does not replace a traditional password vault or an enterprise secrets management system, nor does it manage or rotate application or machine secrets. Teleport issues short-lived certificates for interactive access (SSH, Kubernetes, databases), which helps avoid sharing persistent passwords for human login workflows. Other credential types, including database passwords, cloud API keys, service account credentials, application secrets, certificates, or machine identity keys are outside Teleport’s scope. Teleport does not provide secrets lifecycle controls, automated rotation, policy enforcement, or centralized governance.
The CyberArk Identity Security platform can manage human, machine, and AI agent identities at scale, whether they are passwords, API keys, certificates, or machine identities. This gives organizations a single authoritative system for securing all privileged secrets, reducing sprawl and simplifying compliance, audits, and operational governance.
Teleport’s CLI-oriented model is familiar to Kubernetes-centric developers and DevOps teams. Its integration with tools like kubectl and chat-based workflows can feel natural in those environments. CyberArk supports CLI workflows too, but also provides a web UI and agentless Windows access to accommodate a broader range of users and skill sets. Organizations don’t have to be command-line only to use CyberArk, making it friendlier for consistent enterprise adoption.
CyberArk is designed to operate across heterogeneous, hybrid environments by default. It supports AWS, Azure, GCP, and on-premises infrastructure, including systems that do not support modern identity protocols, through a combination of agent-based and agentless access, credential vaulting, and policy-driven controls. This allows organizations to bring both modern cloud resources and legacy platforms under a consistent privileged access model with minimal architectural change.
Teleport is optimized for cloud-native infrastructure patterns, such as Linux servers, Kubernetes clusters, databases, and internal applications that can participate in certificate-based or proxy-based access flows. Extending Teleport beyond these patterns often requires resource-specific configuration, protocol alignment, or infrastructure changes, particularly for platforms or services that cannot integrate directly with Teleport’s identity model.
For organizations operating across a broad mix of cloud services, on-prem systems, and legacy technologies, CyberArk provides a more consistent and scalable access experience. Teleport may introduce operational complexity when applied across a highly diverse enterprise estate.
Teleport’s architecture does embrace some zero trust principles (like not relying on network location and using short-lived credentials). Eliminating standing passwords is good. However, Zero Trust is broader than just using certificates: it also means continuously verifying user, device, and context, enforcing least privilege at every layer, and implementing broad auditing capabilities. CyberArk’s approach to zero trust is more comprehensive. For example, CyberArk can incorporate device security posture (through integrations or its own Endpoint Privilege Manager) as part of the access decision, ensuring the device is trusted, not just the user identity. CyberArk’s platform also manages machine identities and secrets, which Teleport doesn’t address. Teleport covers one slice of zero trust – ephemeral user credentials – CyberArk helps implement zero trust as an end-to-end strategy from all types of identities to all types of resources.
Grant access with intent.
Leave no standing privilege behind.
CyberArk’s hybrid approach, blending powerful automation with proven security controls, makes it the choice of thousands of organizations looking to protect critical infrastructure without slowing down innovation. If you’re seeking a unified solution for privileged access that scales across all your identities: human, machine, and AI agents, CyberArk is ready to help.
Learn more with our top strategic assets, including a Zero Standing Privilege guide, top analyst research, and customer video.