Remote Access
Provide secure remote access to CyberArk Privileged Access Manager with biometric multi-factor authentication without the need for VPNs, passwords, or agents.

Remote Access
Stay connected and protected
Easily enable secure privileged access for your remote workforce.
Enable Digital Business
Launch privileged sessions directly from browsers or remote connection managers for frictionless and secure workflow
Defend Against Attacks
Remove operational overhead from managing VPNs, agents and passwords
Enhance Operational Efficiencies
Just-in-time provisioning for vendors without adding their identities into AD
Securely work from anywhere
Secure, remote access management in our increasingly virtual world.
Automate sessions from a central location
Deploy VPN-less, password-less, agent-less solution
Just in time provisioning for external vendors
60%
of the US Workforce will be mobile by 2024 *
82%
re-use passwords across devices, applications and systems *
Remote work shouldn’t be unsecure work
Intelligently connect your remote workforce to your business.
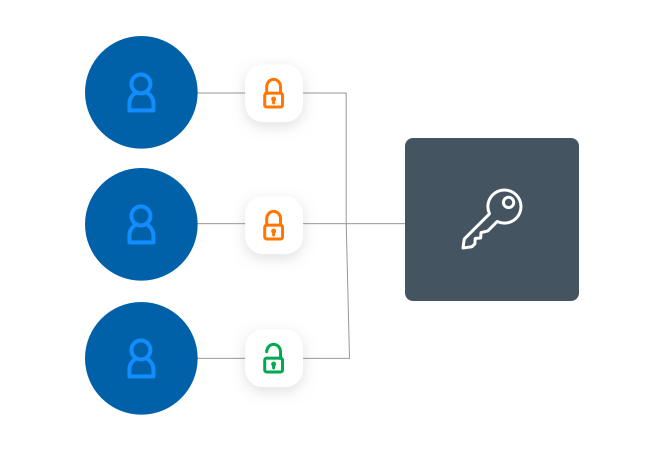
Zero Trust Access to PAM
Ensure remote users confirm their identity each time they require access to critical assets.

Biometric Multi-Factor Authentication
Utilize capabilities of smartphones to confirm identities through inherent authorization methods and dynamic QR Codes.

Integrate with CyberArk PAM
Automatically enforce session isolation, monitoring and recording, without disrupting native workflows.

Just-in-Time Provisioning for External Vendors
Simplify the provisioning process for external vendors who need access to CyberArk PAM: support for direct or delegated provisioning.
Built for today. Protecting your tomorrow.
Explore
related
resources
Get a 30-day trial
Quickly, securely provide access
Experience a frictionless SAAS
Ensure partner productivity
Audit and manage sessions with ease

Sign up now
Every submission is subject to review. Registrants must provide business contact information to be eligible. To better help trial participants, please provide which use cases that are of interest to validate in the “Goals for Trial” field.
*Source: Mobile Workers Will Be 60% of the Total U.S. Workforce by 2024, According to IDC
*Source: CyberArk Survey on the Remote Workforce, Q4 2020
CyberArk Has Patent Rights Relating To This Technology – https://www.cyberark.com/patents