Remote workforce access
Working remotely is no longer optional. Be confident your remote workforce is productive and secure.
Remote workforce access
Feeling secure in a remote world
The risk landscape has shifted drastically in the last year.
Off network
Workers need VPNs and other means to access the corporate network.
Collaboration tools
New communication and productivity tools are adopted quickly.
Non-standard devices
Personal devices are being used for productivity in new and unexpected ways.
3 critical steps to reduce risk associated with remote access
Use these 3 steps to review your security program and priorities for this new reality.
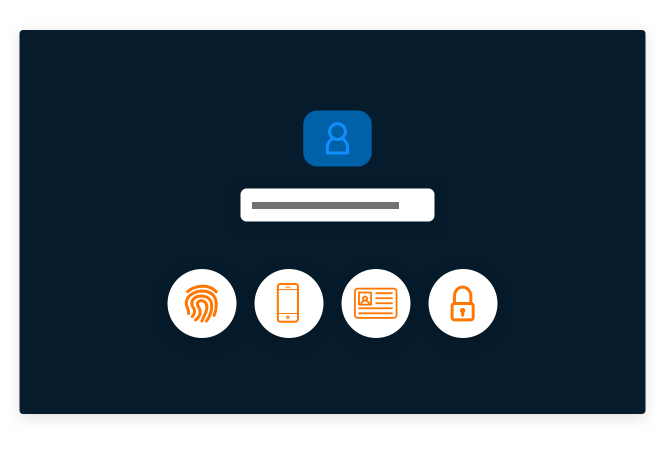
Secure users
Secure remote access for workforce users and 3rd party vendors without requiring a VPN. When you do use a VPN, secure access with Multi-Factor Authentication.

Secure devices
Secure endpoint login with Multi-Factor Authentication and local admin rights with Least Privilege to prevent lateral movement and privilege escalation.
Secure apps
Manage access to applications using Single Sign-On, and secure access to cloud consoles and accounts without relying on shared credentials.

Mitigate the risk of remote workforce and vendor access
Whether your organization must follow standard operating procedures or swiftly execute business continuity plans due to pandemics such as Covid-19, abnormal weather, or any other trigger, it is imperative to reduce the risks associated with the “new normal” of remote users accessing critical systems.
As you review your security program and priorities for this new reality, rely on CyberArk to keep remote users, workstations, and critical assets secure.
Secure remote workforce access
Secure remote users’ access to cloud and on-premises applications, endpoints, VPNs, and other critical resources.
Secure workstations
Explore how CyberArk Endpoint Privilege Manager can help you secure your workstations.
Secure 3rd party vendor access
See how Vendor Privileged Remote Access can secure remote 3rd party vendor access to critical assets managed by CyberArk – no VPNs, agents or passwords required.
Securing work-from-home arrangements
Scale and secure your remote workforce without making it difficult or painful for your employees to work.

“The CyberArk Identity Security Platform is a great tool for providing simple and secure access to our staff. By removing the burden of creating and remembering passwords and offering seamless, one-click access, we are improving productivity and enhancing our security posture.”
John Vincent, Director of Technology, Chico Unified School District

"CyberArk has been the best vendor I have worked with in my 20+ year IT career. CyberArk delivers great products that lead the industry in managing privileged access."
IT Security Manager, Security and Risk Management

"With CyberArk, we are confident that we have implemented technology that will work with us as our business grows and develops."
Jean-Pierre Blanc, Bouygues Telecom

"This isn’t just a compliance check-box exercise, we’re actively designing and aligning policies to cybersecurity best practices to strengthen our overall security posture and align internal teams."
Joel Harris, Manager

"CyberArk gave us the visibility and granular control needed to implement both least privilege and ‘default deny’ application control with minimal disruption to the organization."
Ken Brown, CISO

"With RPA and Cloud migrations, credentials are becoming more and more spread out away from 'normal' controls. CyberArk can spread out to cover all of the scenarios in a standard way."
Information Security Consultant, Enterprise Cybersecurity Solutions Technologies
Explore
related
resources
Contact us about securing remote work
Enforce privilege at the endpoint
Open up secure access for vendors
Control access to applications















