
Introduction
Everyone knows what phishing is. It has been around for more than two decades. Now it seems that phishing is more accessible than before. This blog covers how malicious actors can benefit from the rise of subscription models of phishing, or “Phishing as a Service.”
TL;DR
- Turning the tables: Becoming a hunter instead of prey for phishing attackers, by:
- Entering groups where the attackers are members.
- Finding identification details for the server where all of the groups’ phishing files are stored.
- Easy phishing: How easy it is to use the phishing kit to obtain a lot of personal information.
- Analyzing and aggregating: Summation of various phishing campaigns.
Get the Phishing Link
It all began when we received an SMS titled “Isracard” (this is the name of an Israeli credit card company). The SMS contained the following link https://ow[.]ly/tthX30SiE8w (Figure 1). The link is a short link that references the address https://3fed85ce0a9501496.temporary[.]link/2/ar22/aramex-infos.php
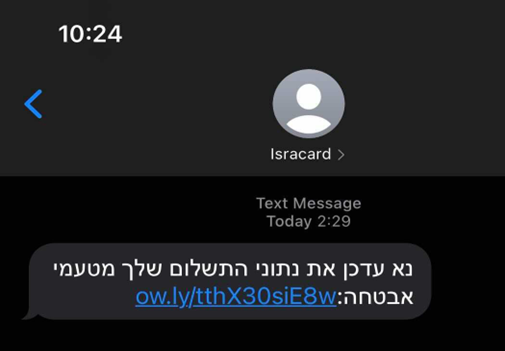
Figure 1: The message says, “You need to update the payment information for security reasons.”
By pressing the link, you reach the following billing page (Figure 2), which looks odd at first glance. It seems the attackers have constructed a mirror page to lure victims into inserting their personal financial details such as credit card details, the security number (CVV) and the card’s expiration date. When the button is pressed, the data is sent to the attacker’s server. After that, the victim is redirected to a site called www.aramex.com.
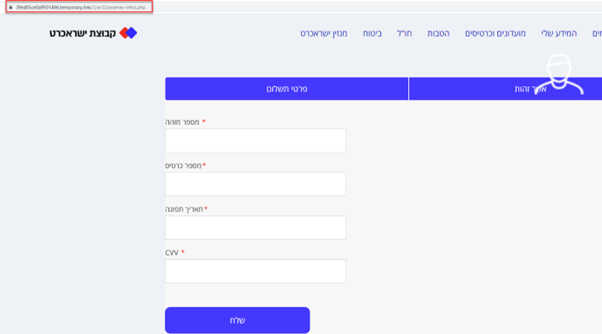
Figure 2: The picture shows us how the page looks.
We sniffed around the mirrored site to see if we could find interesting bits. Lo and behold, we had access to several directories, which you can see in Figure 3. One of the directories, named “2,” allowed us to review its content (Directory Listing). After digging inside, we saw that there was a file archive named “ar22.zip,” which contained the entire phishing package suite.
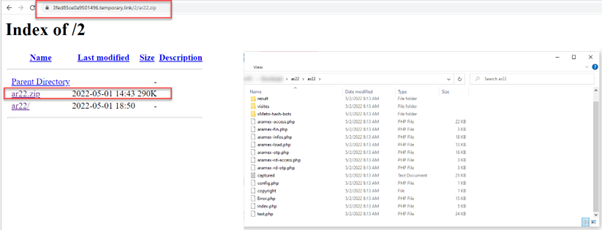
Figure 3: The contents of the phishing package file after downloading and extracting the zip file.
Hunting the Attackers
Almost immediately, we noticed a file named “config.php.” Apparently, these files hold a Telegram bot token (Figure 4). By using this Telegram token, we were able to receive information about every person that was subscribed (Figure 5) to the bot. In other words, we had the details of every group and user of the phishing campaign.
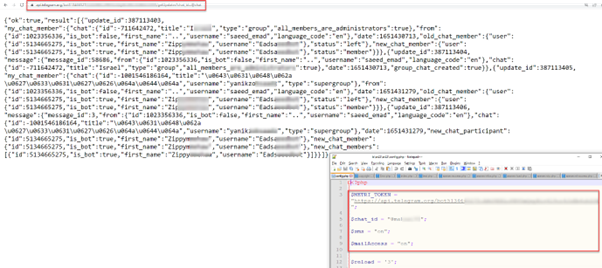
Figure 4: We see the users and groups that are registered to this bot.
We found two channels that were either fully open or possessed zero restrictions upon access. This allowed us to easily review the content without being a member of the group or receiving an invite.
The following information was accessible:
- Chats between the group members
- How and where to buy phishing kits
- Login information to the VPS server (where all the company’s phishing kits are stored)
- Chats regarding the next phishing campaign
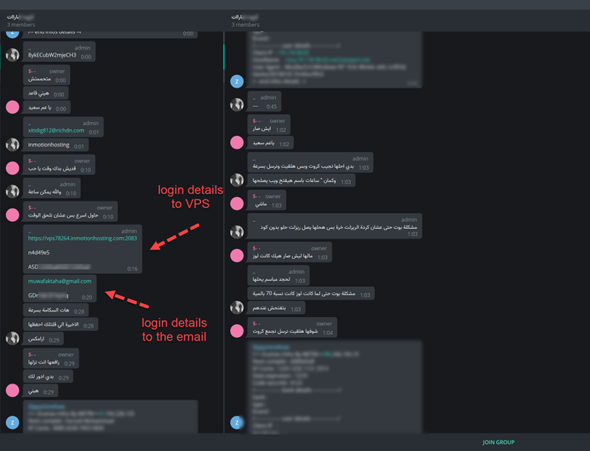
Figure 5: Conversations between group members.
Since we had the login credentials, we were able to connect to the VPS server (Figure 6). In the server, we saw multiple active phishing campaigns, with each kit designated to a different country.
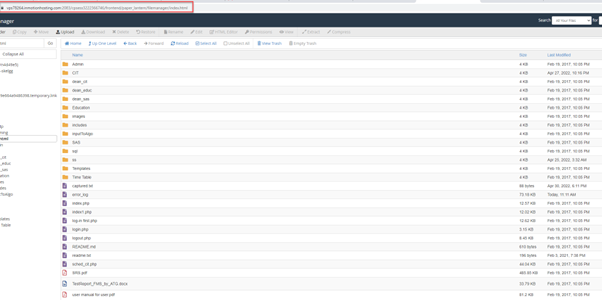
Figure 6: All of the phishing packages this group sent to the victims. Each folder contains a different phishing kit.
Besides that, there were additional phishing campaigns that mimicked the landing pages of known enterprises (Figure 7).
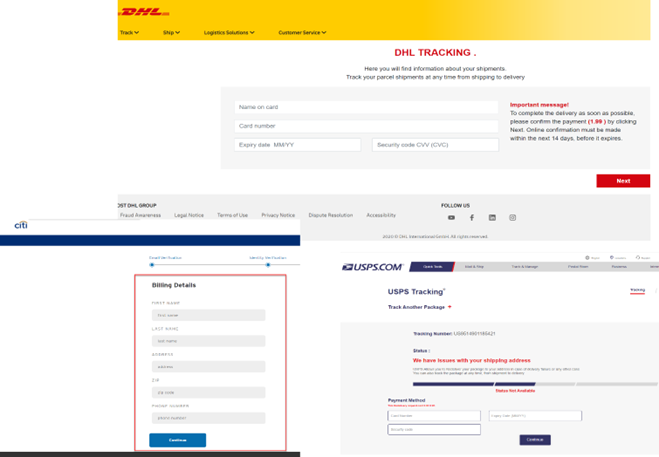
Figure 7: Here are a few of these mirroring sites that we found
Finding Phishing Kits for Sale
After poking around these groups, we found some additional metadata regarding commit messages, comments and emails of those phishing package creators (Figures 8, 9).
Some of the nicks are:
- spoxcoder
- Officiel[.]UGEYO
- Spox DZ
- ARON- []TN
- ITNA1337 (previous nickname Cyb3r_3rr0r)
- Shadow
After searching for the nicks on Telegram, Darkweb and Google, we tracked groups of those creators. These groups had tools and information that could lead to phishing attacks. Here is a list of interesting kits, including:
- Email accounts used to send malicious links
- Phone numbers of potential victims
- Tutorials
- Phishing kits for sale
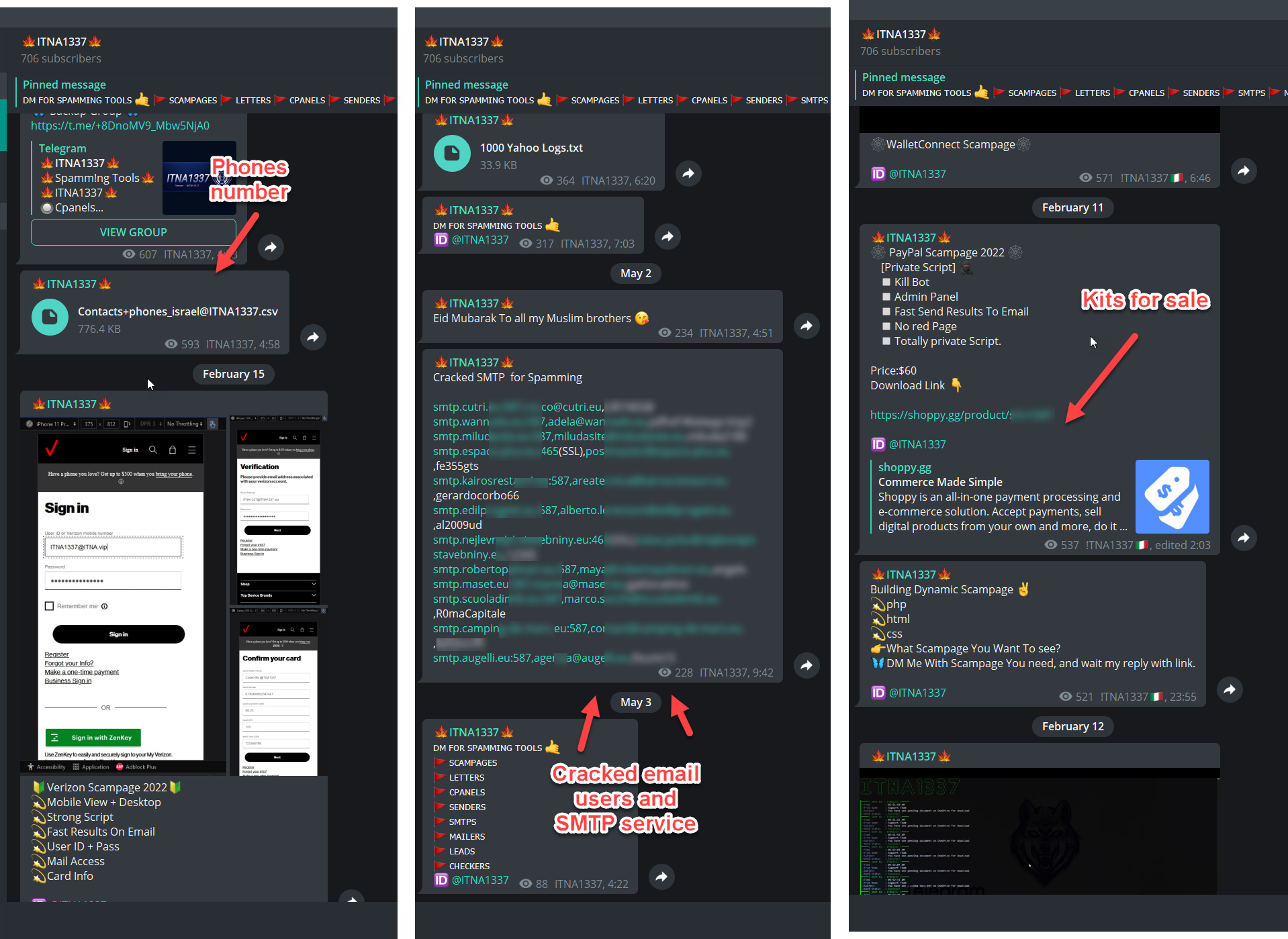
Figure 7: Here are a few of these mirroring sites that we found
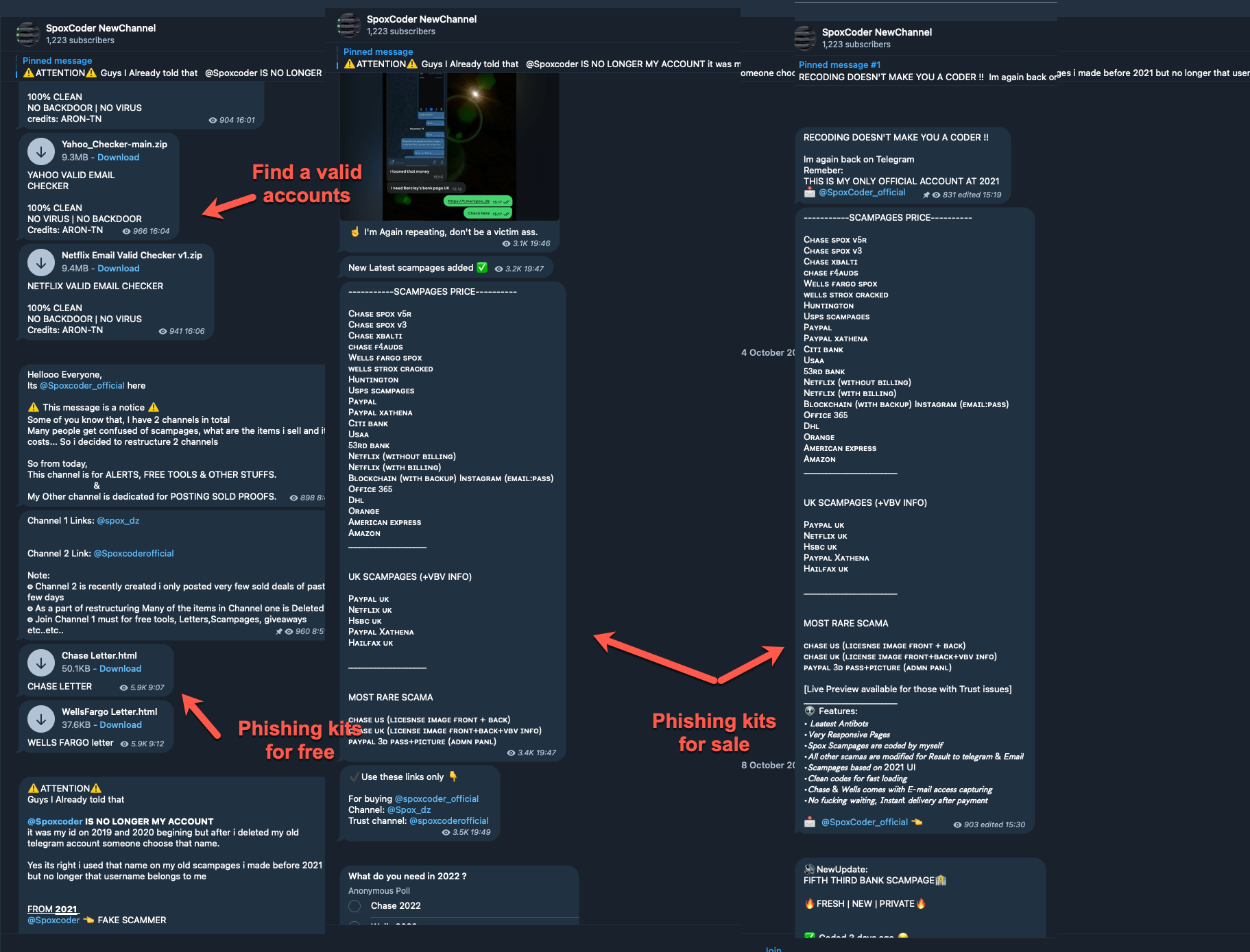
Figure 9: Part of what we found on the “SpoxCoder NewChannel” channel.
Creating Our Own Phishing Attack
During the research, we came to the conclusion that it’s pretty easy to create a phishing attack, and you don’t necessarily need to be a techy person to do so. We decided to create a phishing campaign to demonstrate (Figure 12).
The following items are needed before launching a phishing campaign:
- Server/VPS: Used to store the phishing package.
- Shortened link: Used to hide the actual link from the victims.
- Phone numbers: We found a list of potential numbers on one of the Telegram groups.
To create a server/VPS, we used Amazon’s EC2 service. New users enjoy this service for free for one year.
On the server, we used the Apache service to enable a web server. After that, we uploaded the phishing package from the Telegram group to our server.
To hide the actual address of the server and to shorten the address, we used the bit.ly (Figure 10).
Now that we had a shortened link to the server where the phishing kit was stored, the phishing campaign was ready (Figure 11).
This entire process should take up to 10 minutes.
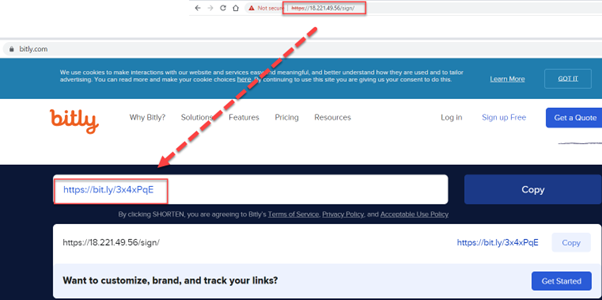
Figure 10: The picture shows the shortened URL of the site.
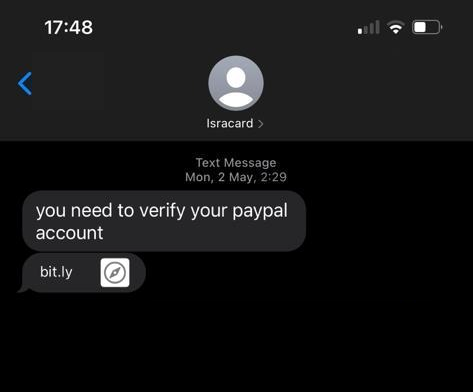
Figure 11: The shortened URL used in the campaign.
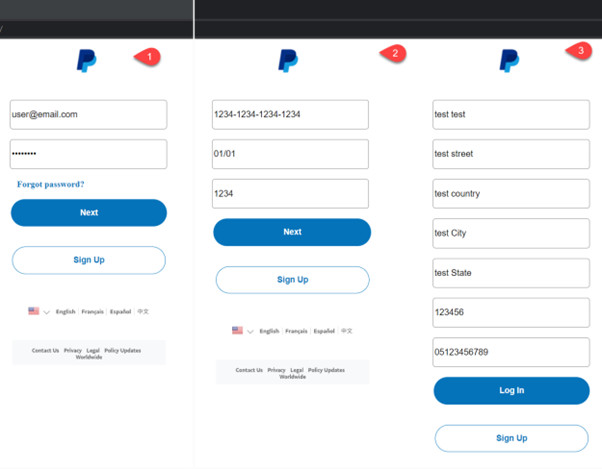
Figure 12: The picture shows the phishing campaign steps.
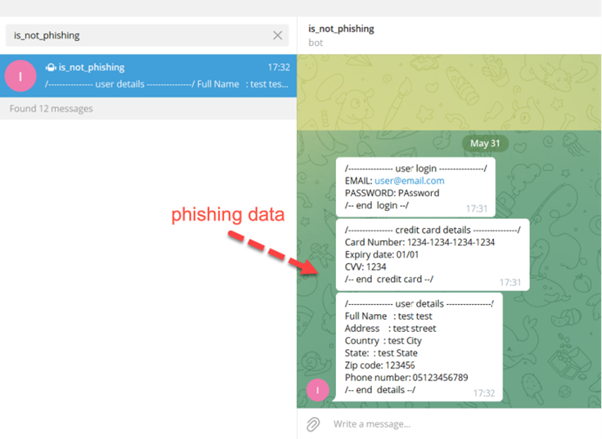
Figure 13: The picture shows us all of the data send to the Telegram group, which we set up for this purpose.
Summary
Let’s talk numbers. This information is based on Telegram groups and log files found on the VPS server belonging to the attackers:
- Israel Credit Company: The attackers gained credit card information from almost 1,200 victims.
- Global bank: The personal information of 450 people, including credit information, login details for the global bank website and social security number, was found.
- Major streaming service: The information of 60 people, including credit card details, site login data and cookies, was found.
After researching several phishing attacks, we came to the following conclusions:
- Most attacks used phishing packages purchased on various platforms, including Telegram, Shopify and Darkweb. No tech knowledge is needed to operate them.
- Due to the problem with SMS protocol, an attacker can send a message with any name they choose. This makes victims believe that the message is legitimate.
Mitigating Phishing Attacks
Here are a few steps to keep you from falling victim to a phishing attack:
- In existing phishing campaigns, victims often need to enter sensitive details, including credit card numbers, social security numbers, cell phone numbers, email and identification information. Companies or services will never ask you to enter sensitive details without a request to change them. So, if in doubt, users should verify with the company to avoid any potential issues.
- Most of the attackers who built the phishing package are not necessarily familiar with the language of the target victims, and they use translation platforms such as Google Translate. Those platforms do not know how to translate accurately. It is essential to take note of unusual information in the text, strange wording, spelling errors and incorrect grammar.
- Most attackers use email addresses and names like services that are known to the victim to send the link. The attacker used this technique to make the victim think it is something legitimate. It is always necessary to look closely at the email address or telephone number that sends the message to see if it seems legitimate. Most organizations use the same email address or number to send information to their clients.In this blog, we analyzed several phishing campaigns (which were found on the server and in a number of links that were sent).
We showed that the attackers were not techies, and as a result, the server was exposed to several security weaknesses, which allowed us to find phishing campaigns.























