Cyber attackers are hitting organizations from every angle — and, increasingly, from inside. According to a 2020 Ponemon Institute study, the frequency of insider threat incidents spiked by 47% since 2018 and the average annual cost to organizations rose by 31% to $11.45M.
While the majority of insider threats can be attributed to employee mistakes or negligence, malicious insiders (i.e. employees or third parties who abuse legitimate access to company systems for nefarious purposes) are difficult to spot. They often operate under the radar for long periods of time and, with the right resources, can take down organizations both large and small. While they’re getting worse in number, insider threats are nothing new.
In the spirit of National Insider Threat Awareness Month this September, here’s a deconstruction of the infamous “Jurassic Park” incident.
The Definition of a Malicious Insider
Dennis Nedry, the lead computer programmer for Jurassic Park, could not meet the profile of a malicious insider more perfectly. Nedry was extremely motived to bring John Hammond’s beloved park into extinction (pun). He’s a disgruntled employee who feels under-appreciated for his work. His motivation was mainly driven by financial gain. It’s teased early on in the story that he’s in some sort of financial trouble, which likely drove him to sell out to Hammond’s biggest competitor for a payout of $1.5M (equivalent to $2,676,093.43 in 2020). Nedry had approximately 18 minutes to shut down security systems, retrieve over a dozen healthy dinosaur embryos and make his way to the east dock to escape the island and collect his fee.
So how does he do it?
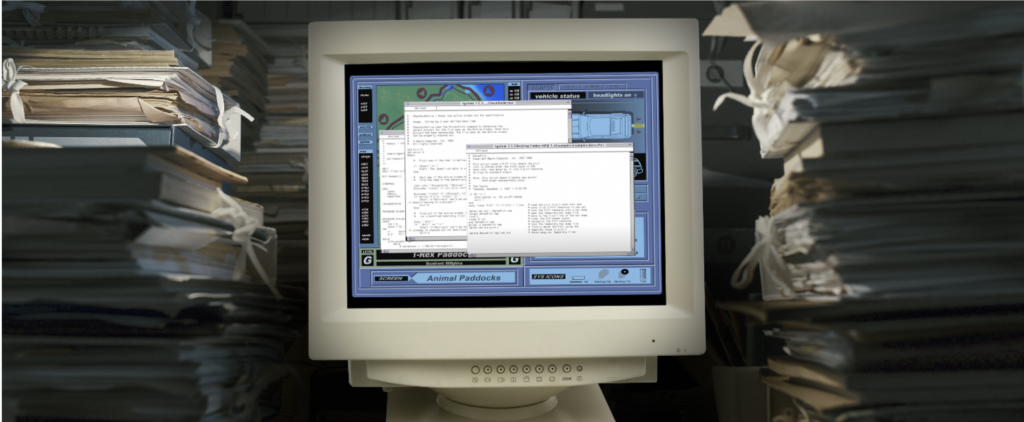
From the movie, we know the park’s control room is equipped with Macintosh Quadra 700s – best-in-class computers in the early 90s. In one scene, the camera zooms in on Nedry’s computer screen, providing a glimpse at three different shells written in an object-based programming language developed by Apple. Believe it or not, someone has reviewed these shells by installing the appropriate OS on an emulator for older Apple systems. Turns out, the shells are just sample code that came with Microsoft Programmer’s Workshop (WPM).
Since these Hollywood theatrics can’t tell us anything, we’ll speculate on Nedry’s attack methodology based on how the movie plays out.
Hold on to Your Butts: An Insider Attack in Action
When chief engineer Ray Arnold tries to bring the systems back online, it’s clear Nedry covered his tracks prior to installing the malicious code. By disabling keystroke logging from the computer, Nedry made it nearly impossible to find it without manually reviewing two million lines of code.
Making matters worse, Arnold can’t crack Nedry’s password to reactivate the security systems. His only remaining option is to perform a manual reboot, which in theory would bring the systems back online – and we all know how the rest of the movie goes.
Let’s dig in a bit deeper and try to break down Nedry’s attack methodology. From the dialogue, we know he is a skilled programmer. He initiated the whte_rbt.obj command from his workstation, which is a piece of code mislabeled as an .obj file type that launched a backdoor attack. Since the same privileged credentials were likely used throughout park systems, the malicious command propagates throughout the park.
To inject this malicious code, Nedry had to do one of the following:
- Write the code onsite, make it executable and run it in an administrative context from his workstation. With his over-provisioned administrative access rights and the park’s poor credential management practices (default password use and credential reuse), we can assume this is a likely scenario.
- Transfer the code from an outside location via removable media, such as a USB drive. Without restricted access policies in place, he could execute malicious code from the Internet.

Privilege was everywhere in Jurassic Park. The central mainframe communicated with all the operational technology components within the park. Because of this, Nedry had complete and total control over not only the digital environment, but the physical infrastructure of the facility including CCTV, doors and, of course, the fences to the dinosaur pens. Judging by personal photos on Nedry’s device, we can assume he is authenticated to all of these systems from his workstation, which has access to external networks and unrestricted removable media — a huge no-no in OT environments, even in the 90s.
Bottom line, there was little to no separation between Nedry’s device (an IT asset) and the critical OT systems in the park. As we recently explored, attackers with access to OT assets can corrupt or shut down critical systems and even put human health and safety in danger. It’s not just science fiction: many of today’s energy, utility and manufacturing facilities rely on these controls to protect their data, employees and customers.
Attackers, Uh, Find a Way: Protect What Matters with Privileged Access Management
Although it takes away from the thrill and excitement of the movie, with the right privileged access management controls in place, Jurassic Park could still be standing.
Beyond standard privileged account and credential management (i.e. vaulting and rotation), the park would’ve benefitted from basic cybersecurity best practices such as implementing the principle of least privilege and attestation for privileged tasks. These would have restricted Nedry’s unchecked privileges to the minimum levels of access, or permissions, required to do his job.
Privileged session management and threat detection capabilities would’ve enabled session suspension and termination when suspicious activities or commands were executed, while maintaining a full audit trail. Additionally, strong application control would’ve ‘deny-listed’ unknown applications and removable media from running, stopping the spread of malicious code throughout the environment. By enforcing these controls, Nedry would not have been able to access multiple systems via a single application and from the same terminal.
Even if Nedry did gain access legitimately using a system like CyberArk Core Privileged Access Security, he would’ve had to enter commands in one at a time. With single, centralized access in place for all systems and endpoints, command restriction and analytics would’ve flagged early warning signs — or terminated his access outright.
Just as life finds a way in Jurassic Park, motivated attackers will find a way – and they are far from the comic relief that Nedry brought to the comparative levity of his actions. In today’s digital world, you must anticipate that malicious characters — both inside and outside your organization — will gain some level of access into IT, OT and even cloud environments. CyberArk solutions are focused on stopping attackers from ever reaching their end target by placing strong privileged access controls around critical resources. Securing privileged access is not chaos theory. Check out our Privileged Access Management Boot Camp or request a demo to get started.






















