
The growing frequency and sophistication of cyberattacks, especially on the ransomware front, have compelled even more companies to seek cyber insurance coverage. But as the need for coverage grows, so do the complexities.
Even though we’re seeing a trend in which premiums have flattened, with expectations that this will continue as a market correction occurs, significant challenges remain for companies seeking coverage. Increased risk profiles are causing insurers to be stricter in their evaluations and underwriting requirements. And regarding controls and processes, what was considered acceptable in past years may no longer be acceptable.
How does this affect your organization? If you’re in the market for cyber insurance, be prepared to answer a litany of pre-audit questions and demonstrate a hardened defense strategy. In this blog post, we’ll discuss cyber insurance trends and best practices to help you be ready.
Top Challenges Shaping Today’s Global Cyber Insurance Market
Rampant ransomware attacks have made cyber insurance a priority for corporate leaders and boards. This epidemic has also changed the equation for cyber insurers’ profitability.
As we’ve noted in past years, many cyber insurance providers have reported massive direct-loss ratios for standalone policies. At the same time, they’ve struggled to adequately cover escalating costs as conditions change quickly. Consider these statistics:
- The average total cost of a ransomware attack increased by 13% to $5.13 million since 2022.
- Nearly nine in 10 security decision-makers say their organizations were targeted by at least one ransomware attack in the past year.
- Almost three-quarters of organizations paid ransoms at least once in the last 12 months.
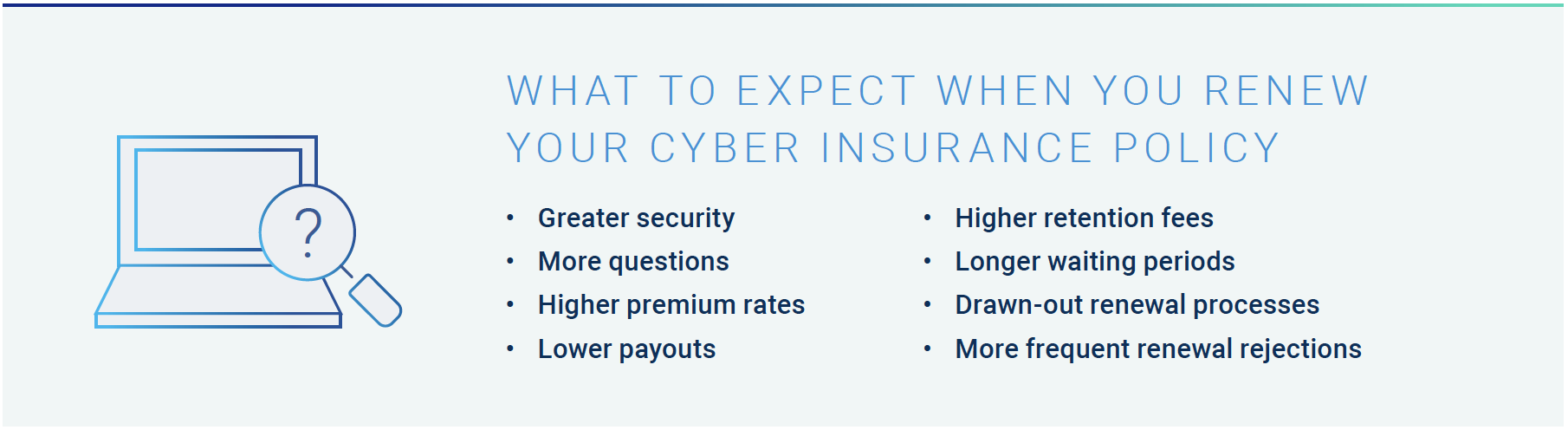
As a result, requirements are becoming more stringent as carriers aim to mitigate risks. This is a significant part of why obtaining a cyber insurance policy with favorable terms, conditions, pricing coverage and low retention has proven to be a struggle for many organizations.
Several years ago, a security team could fill out a brief cyber insurance application and answer a handful of questions. Fast forward to today: the world has changed, as new identities, environments and attack methods reshape what it means to have a strong security posture. Insurers aren’t only considering ransomware risk as they tighten up qualifications – current market volatility and continued geopolitical tensions also factor into the equation.
High-profile incidents such as MoveIt Transfer, Accellion, SolarWinds and Log4j have intensified concerns about software supply chain risks, prompting new questions about aggregation exposure and systemic losses. Meanwhile, global privacy regulations like GDPR and CCPA continue to evolve in a patchwork fashion, and litigation and fines are growing. The average cost of a data breach rose 12.6% to $5.05 million for organizations with high levels of regulatory non-compliance.
Together, these variables fuel even more underwriting questions.
Cyber Insurance Requirements Dig Deep – A Solid Controls Narrative Provides an Edge
Scoring a cyber insurance policy or renewal with the right terms may be difficult, but it’s not impossible. Carriers and underwriters are responding favorably to companies instituting robust security controls and incident response plans — especially those prepared to dive deep into their cybersecurity architectures and planned roadmaps. It’s essential to be proactive in implementing baseline security measures and to articulate a meaningful risk-based approach to cybersecurity.
Underwriters often assess security systems and practices using open-source scanning tools like OpenVAS and OpenSCAP to probe applicants’ networks for vulnerabilities and security rating services like SecurityScorecard and BitSight to evaluate risk. Many underwriters partner with outside cybersecurity firms to vet customers.
Recognizing the challenges organizations face amid stricter vetting, Amazon Web Services (AWS) launched a program to help its AWS marketplace customers find and obtain affordable policies.
During these evaluations, they’re looking for evidence of specific cybersecurity controls and practices, and upcoming audits will examine certain areas more closely than ever. They are:
1. Endpoint privilege security
Since ransomware attacks typically start on workstations and servers, endpoint privilege security will be under the microscope. Initially, insurers wanted to see that a company trained its employees in phishing and credential theft techniques and used endpoint detection and response (EDR/XDR) solutions to help identify and remediate suspicious activity.
Today, even these critical measures are not considered sufficient on their own. Attackers are constantly switching things up and finding ways to turn off or bypass EDR/XDR by abusing administrative credentials, as seen in the SolarWinds attack. This has prompted more underwriting scrutiny around endpoint privilege controls, especially a company’s ability to remove local admin rights from all users — senior system administrators, developers and even people using legacy applications that require admin rights.
To demonstrate effective risk reduction for underwriters, many organizations apply a defense-in-depth mindset by limiting privilege escalation, enforcing application control on endpoints and managing local admin passwords in a PAM solution. Organizations must prioritize between least privilege control and operational efficiency.
2. Multi-factor authentication (MFA)
Requirements for MFA — a checkmark item for insurers until recently — are also growing. Insurers started to dig deeper as more post-payout analyses revealed that MFA wasn’t being fully utilized, particularly in the healthcare and higher education sectors. They found significant coverage gaps for privileged accounts, which are not often linked to a specific person (i.e., the admin account on every server) but are used by system administrators and other privileged users to protect sensitive data.
3. Privileged Access Management (PAM)
As a result, underwriters have started mandating PAM for privileged accounts not tied to specific users (i.e., local admin, root and service accounts) to achieve MFA and isolate high-value assets. Embracing modern use cases for PAM programs – such as the emerging concept of zero standing privileges (ZSP), in which high-risk access is elevated on the fly, restricted to the bare minimum permissions, and protected from malware – can also help prove to insurers that an organization is defending against credential theft.
A defense-in-depth approach can help here too. Aim to apply several layers of control, like enforcing least privilege access on endpoints and in hybrid cloud environments, programmatically rotating credentials and secrets, verifying all access attempts with MFA, and monitoring high-risk access. Again, efficiency is critical – minimizing friction for end users is key to building the adoption of security controls that auditors and insurers want to see.
4. Controls for third-party access
Insurers are also looking at how organizations authenticate third-party privileged users from vendor organizations who need access to sensitive data and company systems. As enterprise reliance on vendors and contractors grows, third-party involvement increases the average total cost of a data breach by roughly 5% to nearly $4.7 million. Vendors require the same security, yet they are rarely given the same security consideration as employees. For instance, if a vendor is onboarded for a brief two-week engagement, they should be onboarded and offboarded following the same HR processes as a new employee to minimize risk. Visibility is also essential.
Organizations should fully isolate and monitor privileged sessions with full audit capabilities – akin to how they secure internal privileged users’ access and actions.
5. Security for non-human identities
The heightened focus on privileged access management extends beyond users to non-human identities, which outnumber human identities by 45:1. These identities could be service accounts, hardcoded secrets or any off-the-shelf or homegrown solution requiring powerful credentials to perform its function (i.e., configuration management databases platforms and DevOps orchestration tools), along with automated processes such as robotic process automation (RPA). As part of this, insurers are looking for stronger privilege controls around automated patch management systems, vulnerability scanners and other existing security tools that attackers may try to disable.
6. People and processes
Beyond technology safeguards, insurance carriers still want to see sound people practices, such as conducting ongoing cybersecurity awareness training. They’ll also evaluate data backup practices and incident response plans to understand how quickly the organization could restore operations in the wake of an attack. Any security program relies on people, practices and technology – and insurers know it.

Steps in the Right Direction: Adopting an Identity Security Approach
As companies prepare for cyber insurance renewals, they should be cognizant that security control requirements are evolving to address the fast-paced world of digital business – and the ever-evolving nature of today’s threats.
Yet accelerated change is always difficult from an organizational and cultural standpoint and can create fear and uncertainty. The best way to minimize this is to ensure people understand the “why” and that risk mitigation controls will not impact operational efficiency. Companies need to spend time on the education factor.
The good news is that more companies are stepping up and taking meaningful steps to bolster their ransomware defenses. As stronger controls are implemented and used more effectively, insurer losses are starting to stabilize and soften the market a bit. We’re not out of the woods yet, but we’re starting to move in the right direction.
As organizations work to meet today’s requirements with an eye on the future, they must focus on effectively mitigating cyber risk without slowing down their businesses.
Today, any compromised identity (human or non-human) can be a gateway to the resources attackers target through tactics such as ransomware. And you’re protecting the enterprise at a time when three realities — new identities, environments and threats — are making the job more complex than ever. An integrated identity security strategy is the best line of defense against attacks in today’s threat landscape, with a unified approach that enforces least privilege and enables Zero Trust.
Organizations looking to close security gaps within a specified period to land or maintain a cyber insurance policy can benefit by aligning with the right security partner. CyberArk can play that role, helping you strengthen security, meet pre-audit requirements, keep premiums down and maintain business velocity. To learn more, check out our cyber insurance resources.
John Natale is a senior content marketing manager and Ryne Laster is a product marketing manager at CyberArk.
Editor’s note: For more on the complex and rapidly evolving world of cyber insurance, check out the CyberArk Trust Issue’s podcast episode, “Cyber Insurance: Managing Risk and Protection,” with guest, Ruby Rai, Cyber Practice Leader, Canada at Marsh McLennan. The episode is available in the player below and on most major podcast platforms.






















