
Since early May, Baltimore has been crippled by a massive ransomware attack that has held many of the city’s IT systems hostage. The attack has effectively “frozen” thousands of government computers, causing everything from real estate sales delays to water bill payment disruptions.
The cyber attackers responsible for the attack have demanded 13 bitcoins — worth about $100,000 – in order to restore these systems. Baltimore City Mayor Jack Young has publicly stated that the city will not pay the ransom demand, but even though the FBI, Secret Service and a host of cybersecurity experts are working around the clock to get things back to normal, new reports indicate the attack will ultimately cost the city more than $18 million.
Just this week, a Krebs on Security post quotes a source who says “it’s not terribly likely” that the Eternal Blue exploit was used to propagate the Robbinhood ransomware, debunking earlier reports that linked the Baltimore ransomware attack to the hacking tool developed by the U.S. National Security Agency (NSA) and leaked online in 2017.
Ransomware Attacks Against State and Local Governments On the Rise
According to the latest Verizon DBIR report, ransomware accounts for nearly 24 percent of all malware-related attacks across industries. Meanwhile, a 2019 Beazley Group breach insights report notes a staggering 105 percent spike in ransomware notifications from the first quarter of 2018 to the same period this year. Payment demands are also increasing significantly. The Beazley report indicates that the average payment in the first quarter of 2019 – $224,871 – has already far-surpassed 2018’s total of $116,324.
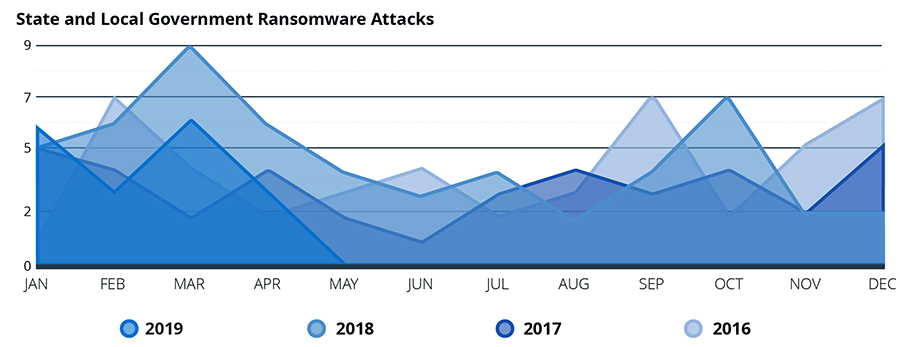
As evidenced by the Baltimore attack, state and local governments seem to be particularly vulnerable to ransomware. Cybersecurity research firm Recorded Future recently published an interesting study on the surge in state and local government ransomware attacks targeting essential infrastructure and processes, which revealed that reported attacks on state and local government skyrocketed by 39 percent in 2018. Some additional findings include:
- At least 169 county, city or state government systems have been attacked since 2013, including at least 45 police and sheriff’s offices.
- These attacks hit 48 out of 50 states, as well as Washington D.C.
- Twenty-four of these attacks were against local school systems or colleges.
- The primary ransomware families used for ransomware attacks in the past 24 months were GandCrab and Ryuk.
- Many of these attacks were opportunistic: In many cases, attackers “stumbled” upon public-sector entities when looking for vulnerable targets. However, once they were identified, the attackers focused on these targets, recognizing the potential for notoriety and heavy media coverage.
Since the conclusion of the Recorded Future study in April 2019, several new ransomware attacks against state and local governments beyond Baltimore have made headlines – from Lynn, Massachusetts to Cartersville, Georgia. It’s safe to say that these types of attacks are not going away any time soon.
Four Tips for Mitigating Risk of Ransomware Attacks
While there is no silver bullet for ransomware prevention, there are a number of steps government agencies and enterprises alike can take to dramatically reduce the risk of malware, such as Robbinhood, from spreading and wreaking major havoc.
- Backup all critical data. Sure, it seems like cybersecurity 101, but it’s amazing how many organizations don’t do this on a regular basis. Prioritize data that is critical to your organization and consistently back it up so that if files are locked and held for ransom, you can still keep (at least parts of) your business running.
- Never stop patching. Consistently patching endpoints and servers will dramatically reduce the attack surface, making a compromise far less likely. If you haven’t already, stop what you’re doing and immediately disable the (very) outdated Microsoft SMB protocol version 1 or apply patch MS17-010. And don’t stop there. Patch all vulnerable software regularly to help prevent ransomware infections – and make sure your antivirus, firewall and other perimeter protection tools are always up to date.
- Beware of phishing. According to the Verizon DBIR report, phishing is involved in 32 percent of today’s breaches and 78 percent of cyber-espionage incidents. Attackers often begin their malware attacks through targeted phishing campaigns. If you receive an unsolicited call, email, text message or chat, do not respond or click on any links – even if the person claims to be from a legitimate department – before confirming legitimacy.
- Remove local admin privileges to contain and block attacks. While employee education around phishing is important, it cannot stop there. Removing local administrator rights is the foundation of effective endpoint security. By implementing a combination of least privilege and application control policies on endpoints and servers as part of a larger Zero Trust approach, you can mitigate the risk of malware like Robbinhood spreading from its initial infection point. Based on testing by CyberArk Labs, the removal of local administrator rights, combined with application control and greylisting, was 100 percent effective in preventing ransomware from encrypting files.
Traditional antivirus/next-generation antivirus or endpoint detection and response solutions cannot block ransomware on their own. CyberArk Endpoint Privilege Manager adds a critical layer of protection to strengthen your organization’s existing endpoint security toolset, allowing you to contain attacks, such as malware and ransomware, at the endpoint. With out-of-the-box policy definition for ransomware protection – including comprehensive least privilege controls tested on hundreds of thousands of malware samples – you can effectively block the spread of malware across your network, dramatically reducing remediation time and effort.
Don’t wait until your organization is front-page news and locked out of critical systems. Take proactive steps to protect privilege on the endpoint and contain attacks early in their lifecycle. Learn more in our solution brief or in this short video.























