
Crypto scams are skyrocketing: In 2022, the FBI tracked an 183% year-over-year increase, driving $2.57 billion in losses. Last week, the popular YouTube channel Linus Tech Tips (LTT for short) – and two associated channels – became the latest crypto scam victim and unsuspecting accomplice. In this video, host Linus Sebastian gives a first-hand account of what went down – highlighting the dangers of cookie hijacking and the need for stronger endpoint privilege security protections across the board.
Recapping the LTT YouTube Account Takeover
Based on news reports and Sebastian’s explanation of the LTT attack, here’s a quick recap:
- An LTT content editor opened a PDF email attachment that appeared to be work-related.
- Within 30 seconds, the attachment – actually malware – dumped all the information from both Chrome and Edge browsers on the machine, including web session tokens. Also known as cookies, these are used to authenticate a device or browser and enable users to stay logged into websites.
- By hijacking these cookies, the attacker was able to do everything from bypassing password and multi-factor authentication login prompts to mass-deleting existing videos, changing channel names and live streaming a crypto scam video.
- After numerous attempts to shut down the scam videos, LTT finally restored control of the channel with YouTube’s help.
Cookie Hijacking: It Gets the Job Done
Cookie hijacking isn’t a new or sophisticated attack technique for gaining access to a corporate environment, but it gets the job done. Especially now that web-based applications are ubiquitous, attackers and credential-stealing malware often go after browsers (which seemingly know everything about us). They recognize that there’s no need to attack domain controllers anymore when targeting browsers – treasure troves of stored credential data (URL/username/password combinations) and session cookies – are just as effective and take far less effort.
Most cyberattacks require some privileged access but not cookie hijacking. CyberArk Labs researchers demonstrated in 2022 that session cookies could be extracted effectively by a standard process running on the endpoint machine. In other words, any program or script that’s executed by a standard business user (or an attacker pretending to be one) can access the security tokens and credentials stored in the browser. This is critical as the session tokens stored by browsers in cookies are post-MFA and long-lived, meaning one can use them to bypass MFA mechanisms and access cloud services and on-premises applications.
Efforts to address this are detailed in CyberArk Labs’ GO BLUE! manifesto, which further underscores the challenges organizations face in defending against attackers who manage to log into devices as legitimate users.
Phishing, Human Error and the Endpoint Privilege Security Safety Net
As so many do, the LTT attack began with spear phishing. Many point to cybersecurity training as the answer. While this can help reduce the number of successful phishing attacks and speed up response times, even the best cybersecurity education can’t change the fact that people make mistakes. When they do, technology should be there to step in, bridging that gap and minimizing the impact of human error.
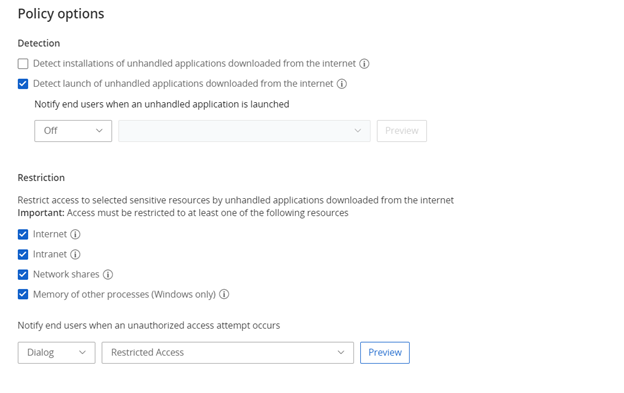
In the case of LTT, a piece of malware was downloaded from the internet and executed on an endpoint machine. Instead of pointing fingers and placing blame, proper endpoint privilege security controls work in concert to identify malware and block it from running in the first place.
With the right endpoint privilege management approach, a mistake will remain a mistake. Not an “end of all,” or a “We are writing to notify you of a cyber incident” event. Just a mistake.
This is not the first nor will it be the last time we see a major social media account takeover. But this LTT attack stands out for its leader’s unusual response: Sebastian lifted a veil for the community by demonstrating how quickly things can spiral and why a technology safety net is required to protect from attacks like cookie hijacking. This attack trend continues to grow in popularity and demands our attention.
To see a cookie hijacking attack through the eyes of an attacker and explore mitigation best practices, check out this on-demand webinar hosted by CyberArk Labs and the Red Team.























