
Trust – how to build it, how to strengthen it and how to restore it – was a major theme at RSA Conference 2022.
Members of our CyberArk team joined 26,000 attendees online and in San Francisco as the Moscone Center once again opened its doors for the 31st annual cybersecurity conference. Reunited in person at last, there was much ground to cover. Yet every hard-hitting issue ultimately came down to trust. That same week, our CyberArk Labs team set out to explore a possible link between trust and consumer cybersecurity behaviors – but more on that in a minute. First, here are some key trust takeaways from RSA.
Trust Takeaways from RSA Conference 2022
Society’s ever-increasing reliance on technology continues to push digital advancements further and faster. Each new day brings another 2.5 quintillion bytes of data and equally as many new opportunities for cyber attacks that can expose sensitive data, breach confidentiality and damage reputations and bottom lines.
“We are more vulnerable because of the dizzying pace we are adopting technology, engaging in tech transformation and adding devices without prioritizing security,” noted Niloofar Razi Howe, an RSA keynote moderator and senior operating partner at Energy Impact Partners. This pattern of “innovate now, secure later” not only drives up cybersecurity debt and puts organizations at greater risk, but it also contributes to a broader cycle of public distrust.
Consumers are more skeptical than ever about how their sensitive financial, genetic, health and location data are used, and privacy concerns continue to grow with every headline-grabbing cyber attack. As U.S. Cybersecurity and Infrastructure Security Agency (CISA) director Jen Easterly noted in the “Cybersecurity as a National Security Imperative” panel, “Building trust is hard, and breaking trust is easy.” During the keynote “Building Trust in a Zero-Trust World to Confront Tomorrow’s Cyber Threats,” Howe pointed to the 2022 Edelman Trust Barometer, a global study of more than 36,000 people that found nearly six in every 10 respondents said “distrust” is now their default state.
Diminishing consumer trust is also fueled heavily by information disorder – the topic of the final keynote, featuring former CISA director Chris Krebs, Color of Change President Rashad Robinson and journalist Katie Couric. As the “slope of discord” seemingly grows steeper by the day, the panel sounded the alarm on how malicious cyber actors can use disinformation and misinformation to their advantage, emphasizing the need to ensure “truth actually has a fighting chance,” to quote Robinson.
The previously mentioned Edelman study shows that people have particularly high expectations of businesses in breaking this cycle of distrust. Numerous speakers throughout the week urged that meeting these expectations – while preserving trust across highly interconnected IT environments and supply chains – means businesses must transform to stay ahead of cyber threats.
Technology plays a big part in these transformation efforts. For instance, Jane Horvath, chief privacy officer at Apple, spoke of privacy-enhancing technologies that focus on data not tied to individual identities, while advancements in telemetry, automation and AI were widely touted as critical to combating ransomware at scale. But don’t confuse technology with broader security approaches, cautioned speakers, including national cyber director Chris Inglis, who made a point of defining Zero Trust as a “digital architecture compromised of technology, of people and practice doctrine.”
Even with the best frameworks and defense-in-depth technology layers in place, businesses can’t shoulder the burden of trust on their own. In her RSA talks and in an op-ed published the same week, Easterly stressed that “cybersecurity requires a whole-of-government and whole-of-society effort.”
Could Trust Impact Consumer Cybersecurity Behaviors?
CyberArk Labs cracked Wi-Fi networks across San Francisco to find out.
Our CyberArk Labs team wanted to better understand if overarching trust issues have influenced consumers’ home Wi-Fi cybersecurity practices. With hybrid work models here for good, unsecured home networks pose serious risks as threat actors target them to steal bandwidth, launch man-in-the-middle (MitM) and other attacks and even pivot into corporate networks.
So while the world talked security at the RSA Conference, our own CyberArk Labs technical evangelist Andy Thompson took to the hilly streets of San Francisco. The plan was this: “war-drive” around densely populated areas to test wireless network resiliency in the U.S. tech capital.
Historically, cracking Wi-Fi passwords is a time-intensive process requiring threat actors (and threat researchers) to intercept a four-way “handshake” as a network connection is established in real time. But thanks to the work of a researcher known as “atom,” there’s a much easier way to pinpoint weak passwords – and it can be done at any time. This PMKID hash harvesting method simply requires the person to be in the vicinity of a home or business router. (Explore all the technical specifics on the CyberArk Threat Research Blog.) Behind the wheel of a rental car, armed with simple, readily available Wi-Fi sniffing equipment – a laptop running Linux and a $50 wireless network interface card – Thompson set out to replicate similar experiments conducted by CyberArk Labs in Tel Aviv and Dallas, Texas.
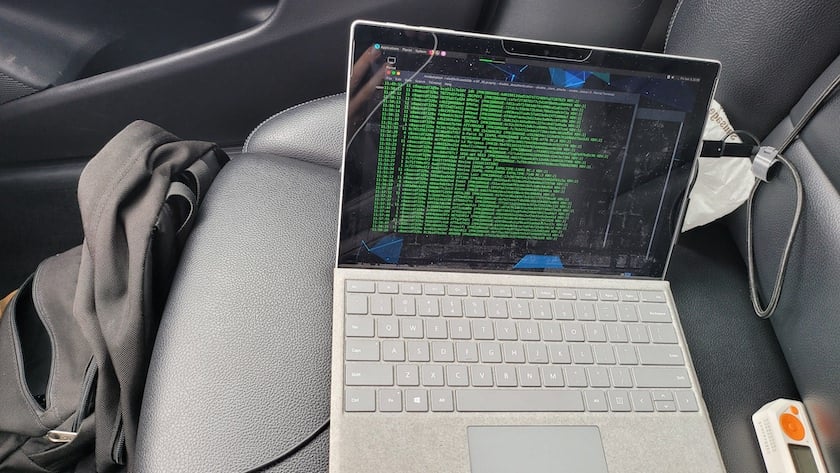
Figure 1. Readily available Wi-Fi sniffing equipment
Twenty hours and countless cups of coffee later, Thompson had collected 5,000 Wi-Fi network hashes, which were sent through CyberArk Labs’ monster brute-force cracking rig (8 x QUADRO RTX 8000 48GB GPUs) that can guess commonly used and weak passwords in seconds or less. It’s important to note that at no point were actual passwords captured or used during this research project.
And the results? Just 6% of the sniffed Wi-Fi networks were crackable in the San Francisco Bay area, compared to 9% in Dallas and a whopping 70% in Tel Aviv. This makes San Francisco the most secure city in our war-driving journey to date and perhaps signals a broader shift in consumer cybersecurity habits and heightened awareness around data protection responsibilities.

Figure 2. Wi-Fi cracking through the hills of San Francisco
Protect Your Wi-Fi Network This World Wi-Fi Day (and Every Day)
With World Wi-Fi Day on June 20, we encourage every online user to consider how they secure this household technology – especially now that it’s used so interchangeably for personal and work life. Because Wi-Fi sniffing activities are undetectable, security safeguards such as two-factor authentication won’t stop them. Instead, it’s important to follow these steps to protect yourself and your employer from Wi-Fi cracking attempts:
- Change the default username and password of your router if you haven’t already
- Update your router firmware and always keep patches up to date
- Upgrade to the WPA3 encryption protocol to help strengthen protections against brute force password cracking attempts
- And most important, use strong passwords that are complex, unique and changed (or rotated) frequently
Protecting our digital identities is a shared responsibility. To echo Director Easterly, every one of us – as individuals, organizations and government entities – must put and keep our “shields up” to strengthen collective defense and trust.
Trust … it’s something we’re talking about a lot these days. Listen to the Trust Issues podcast on Spotify, Apple Podcasts, Amazon Podcasts and Google Podcasts – or wherever you get your podcasts.























