My team and I were on a call with a customer who saw a critical need to secure access to his company’s cloud service provider (CSP) containers. Our conversation comes to mind often, because it reflects the fast-evolving nature of privileged access and what it takes to secure it in today’s complex IT environment.
As we spoke, the customer stood out to me as a forward-thinking leader. His job: protect and enable an enterprise that is no stranger to the cloud. While more than eight in 10 IT leaders are adopting a hybrid cloud environment, this customer’s company was born there. Our job: help him finalize an integrated set of solutions and controls to protect his CSPs.
Our discussion about applying zero standing privileges, or ZSP, to cloud power users – was capturing everyone’s imagination and attention, even my own (and I talk about these things quite a bit). Why? Consider what’s at stake. The risk of having standing access to highly privileged administrative roles is too high. Attackers who compromise cloud users’ identities can disrupt operations, steal data and more.
With ZSP, users are elevated just-in-time (JIT), with only the entitlements necessary for the task at hand. In turn, ZSP enables security teams to secure their cloud environments by:
- Reducing the risk of credential theft by preventing standing access.
- Enforcing real-time least privilege in the cloud by granting only the relevant permissions a user needs – and only when needed – for a given task.
- In turn, lessening the potential impact of an account takeover; an attacker’s options are extremely limited without admin-level access.
PAM’s Essential, Foundational Role Goes Next-Gen
As we dug deeper into how we could help our customer with contemporary use cases – like securing access for cloud engineers and non-human identities – we still needed to talk about the essential role of foundational privileged access management (PAM) controls. Because whether you’re a 100-year-old corporation migrating to the cloud, or a 1-year-old startup native to the cloud, you face a set of constants:
- Your organization has privileged users, accounts and credentials.
- Attackers will try to compromise these users’ identities, move laterally and elevate privileges.
- These users, including IT admins of all types, require fierce protection.
Considering those constants, we wouldn’t be doing our jobs if we didn’t ask the question: “Have you thought about the need for fundamental PAM controls like securely storing and rotating the credentials of highly privileged users?”
The response: Crickets. At first.
Some key “ah-ha moments” arose as we continued exploring our customer’s challenges. For example, securing privileged credentials actually transcends both PAM’s well-established and next-gen eras. It’s a key example of a PAM mainstay that can and should be reimagined, to secure a broad range of high-risk users.
Think about the textbook-definition privileged IT users that companies’ PAM programs have focused on for years – like Linux admins who use SSH keys to access their organizations’ systems. The risk we’ve all seen, time and time again: these admins often store their credentials locally on workstations, where attackers can easily find them.
But you know who else does this? Cloud developers.
Redefining PAM for Today’s and Tomorrow’s Threats
Similar to traditional IT admins, it’s common for cloud developers to download an SSH key from a console, save it on their workstations and use it to log into an Amazon EC2 instance in their organization’s cloud environments. Why? The need for speed leads to risky actions. Regardless of their job descriptions, power users in the cloud are bound by urgency. This is true for:
- Architects under deadline pressure to complete lift-and-shift migrations.
- Developers collaborating in the cloud to continuously build and maintain apps.
- On-call engineers ready to fix any cloud outages that would impact application users.
Enterprises know that every new service rolled out by CSPs comes with a host of new roles and entitlements – with which their existing identity and access management controls are often incompatible. To avoid the problem, they simply give cloud users far more entitlements than they’d ever need – in the name of speed and convenience.
The result: identities are over-permissioned beyond what their roles require and often have powerful standing access. Threat actors know all of this – to the point that the National Security Agency (NSA) suggests misconfigurations are the most common and easiest entry point into cloud environments for attackers.
And like many security leaders, our customer knew it too.
By the time the conversation wrapped up, he was keen to incorporate a balance of reimagined PAM controls like ZSP and time-tested PAM fundamentals into his plan – to the point where he asked: “Why wouldn’t we apply these controls to securing our users’ credentials?” His question applied not only to his cloud users, but to the traditional IT admin roles found within any enterprise of any size, industry or cloud maturity. Because he knew that securing identities in a fast-changing field like PAM means keeping an eye toward the future, while never forgetting the fundamentals.
What One Security Leader’s Story Can Teach Us About PAM’s Evolution
Today’s PAM programs face an increasingly vast and dynamic threat landscape, upended by innovation and reshaped by new identities, environments and attack methods.
Technology shifts have allowed organizations to delegate powerful access to anyone or anything. Any human identity can gain high-risk access, from admins and vendors to cloud engineers and developers. Even the day-to-day business user can now perform admin-level tasks in their domain. The same goes for non-human identities, including automation accounts found in manufacturers’ operational technologies. Moreover, privilege moves with IT. While IT will always exist on-premises, privilege is increasingly in the cloud.
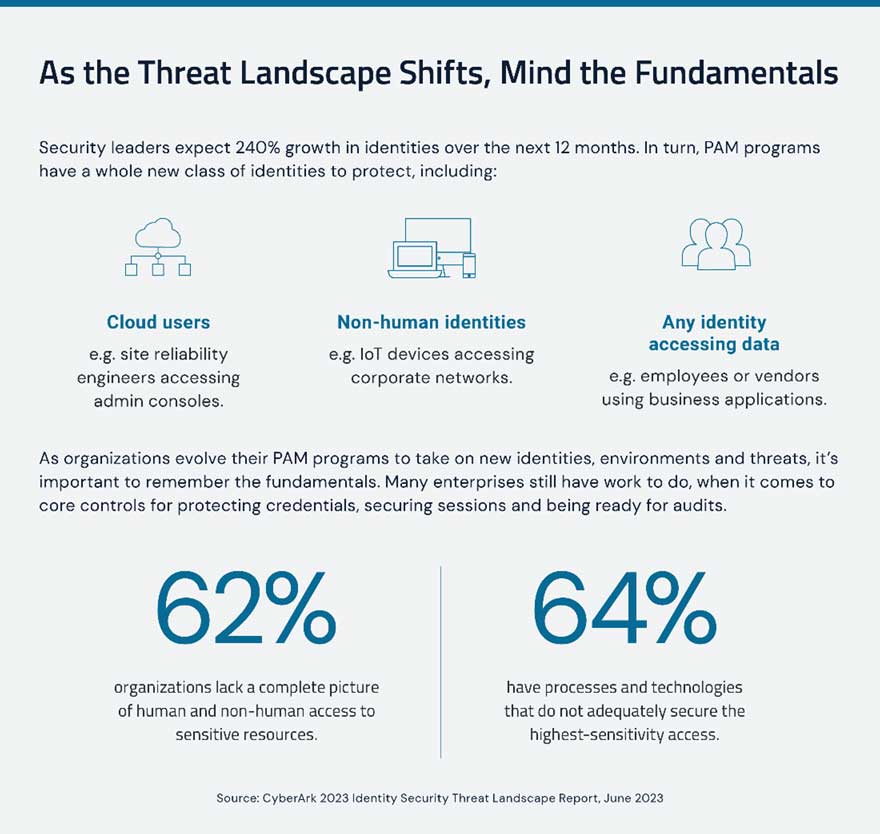
In times like these, PAM is more important than ever – and should be as consistent and dynamic as privilege itself. Organizations will always need foundational PAM. At the same time, IT security teams need to reimagine their PAM programs. Nearly all (99%) security decision-makers say they’ll face an identity-related compromise in the year ahead – with the number-one reason being transformational initiatives like cloud migrations.
Securing Privileged Access in Transformative Times
In a new perspectives piece, I explore two use cases requiring a mix of time-tested principles and innovative new controls.
- The first area is privileged access in cloud environments – we only scratched the surface here regarding the risks and how to secure access for not only human but also non-human identities. Only 25% of security leaders say they secure sensitive access to bots and robotic process automation (RPA) that are integral to cloud-based development – we’ll talk more about how to solve problems like these.
- The second area is operational technology (OT). About 70% of business leaders who’ve invested in securing OT (which includes devices, machinery and systems used in sectors such as manufacturing, energy and healthcare) face implementation challenges. And the stakes are high, especially in critical infrastructure sectors where an OT attack can jeopardize critical services that society relies on. We’ll share best practices on that, as well.
For further insights on today’s fast-changing threat landscape and what it takes to protect your organization, check out Barak Feldman’s viewpoints piece, “Securing Privileged Access in Transformative Times.”
Barak Feldman is senior vice president of privileged access management (PAM) and identity security at CyberArk.























