
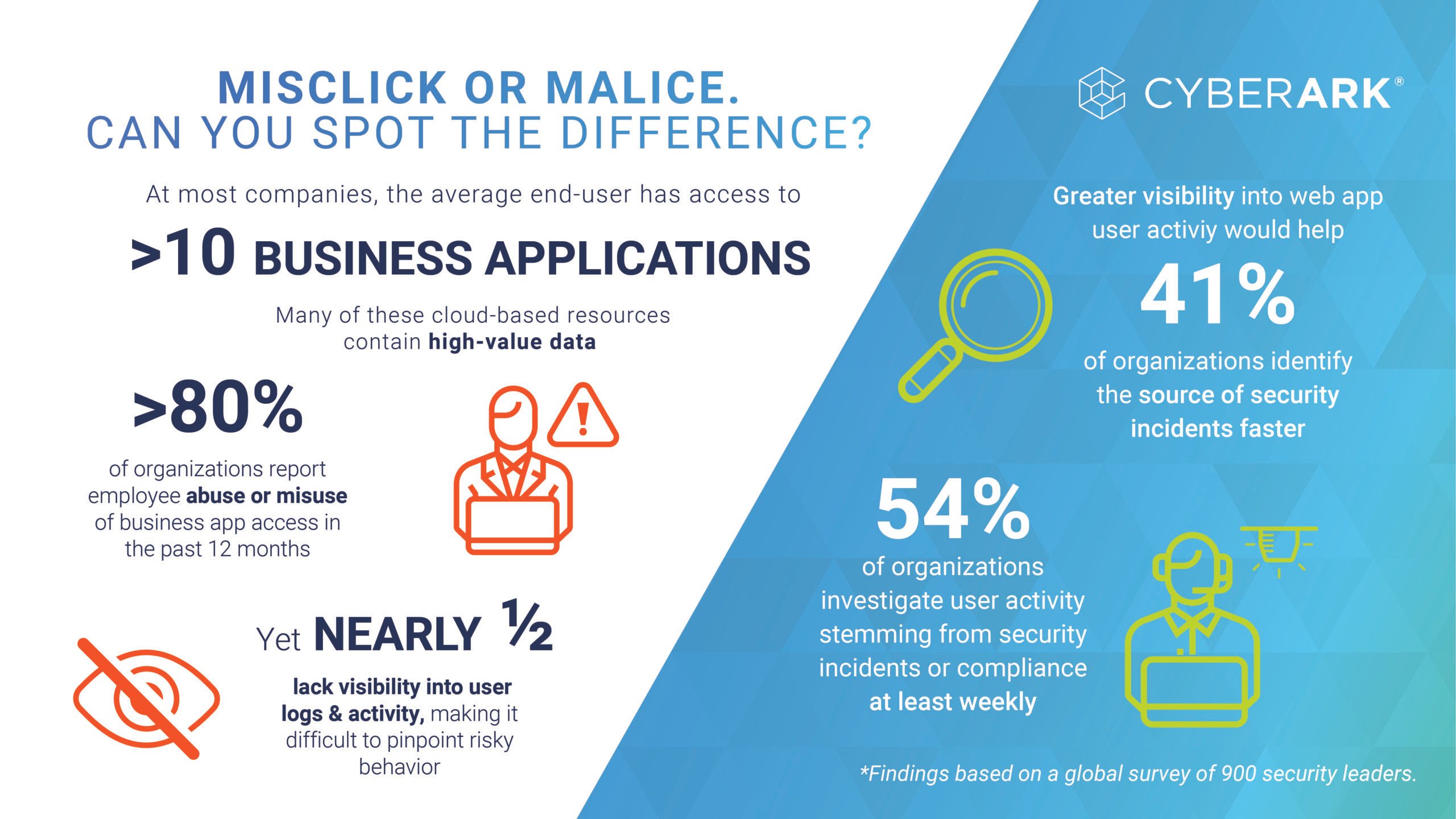
Employees across finance, sales, HR, marketing and virtually every other business department need access to web applications to do their jobs. In fact, new CyberArk research found that in a majority of organizations (70%), a typical business user has access to more than 10 business applications, many of which contain high-value data such as financial records, customer information and intellectual property.
So what happens when an insider uses this legitimate access to obtain confidential data or change something he shouldn’t? Eighty percent of organizations have been in this position — forcing security teams to race against the clock to find out what happened.
In most cases, insider misuse or abuse of application access is unintentional. But making a fast, informed determination between an honest mistake and risky behavior is easier said than done. Investigating user activity takes a trifecta of time, resources and tools — things security and compliance teams don’t always have. And since built-in security controls vary wildly between applications, security teams struggle to consistently enforce strong controls across hybrid IT environments.
CyberArk Identity Secure Web Sessions, the newest addition to our Software-as-a-Service (SaaS) portfolio, helps security and compliance teams unmask and address insider threats and errors quickly by adding extra layers of security to web application sessions. Here’s a look at three real-world industry examples of Secure Web Sessions in action.
Protecting business-critical applications from insider errors and abuse at a high-growth tech firm
Like many organizations, tech companies often struggle to maintain visibility across their fast-growing, highly distributed employee bases. This makes it difficult to understand which end-users are accessing business-critical web applications, when they’re accessing them, and for what purposes.
For example, if someone in the finance department with elevated access rights made a mistake when using a payroll system that led to unauthorized payroll changes, the team would have to sift through thousands of lines of logs and recreate every step the user took to understand what happened.
With CyberArk Identity Secure Web Sessions, these teams could see exactly what happened in that web session and easily trace unauthorized configuration changes within a protected app down to a click. It also makes it easy to search any recorded session for specific keywords or actions to further focus and accelerate the investigation.
Safeguarding sensitive financial data on the trading floor with continuous authentication
Stock traders use multiple devices and applications on trading room floors to save time and gain deeper insights into pricing fluctuations, market data and other critical information. They’re also constantly moving around – not often tied to a desk. It’s easy to imagine a scenario in which a trader steps away from a device during an in-progress web session, inadvertently exposing sensitive information to data loss, fraud or abuse.
In this scenario, CyberArk Identity Secure Web Sessions could help to protect sensitive financial data from unauthorized access by monitoring the trader’s web application usage. If and when they walk away from an open highly-sensitive session, Secure Web Sessions will automatically log them out and prompt re-authentication. Meanwhile session recording and attribution help drive greater accountability.
Continuously verifying that the person who initiated the web session is the same one using the application is an authentication challenge shared by organizations across industries. Nearly 41% of all organizations said that better visibility into user activity would enable them to identify the source of a security incident more quickly, while 38% said it would help them provide more comprehensive reporting to auditors.
Securing patient medical records by restricting data copying and downloading
Doctors and nurses regularly update various patient records throughout the day, while connecting with a host of other IoT devices that record data from heart rates to prescription dosages. Ransomware and other malicious actors are zeroing in these devices, hoping to infiltrate them and progress their attacks toward target systems and sensitive PII.
According to our research, 43% of healthcare providers lack the ability to monitor and audit most of their business apps that contain high-value data. With CyberArk Secure Web Session, healthcare organizations and hospitals can further protect their applications, patient data and users with application-specific session protection. Secure Web Sessions adds local hardening layers to the sensitive web session, protecting it from dangerous actions. Optional integration with CyberArk Endpoint Privilege Manager helps to prevent access from malicious processes, even if running on the user’s endpoint device. Doctors and nurses can continue to safely access protected applications — while admins can know that their session and customer patient data is secured.
Previously, the only way to achieve a similar protection was to configure each application to use streamed browser sessions, a process difficult to scale that often results in dangerous latency issues. Since all protections and recordings run transparently in the background, healthcare providers can enjoy a secure, frictionless user experience and stay focused on what matters most: delivering the highest level of patient care.
Secure High-Risk User Activity with CyberArk Identity Secure Web Sessions
Secure Web Sessions is an add-on capability to CyberArk Identity Single Sign-On and serves as an authentication factor for accessing protected web applications. Request a free 30-day trial and discover the many benefits of simplified, context-aware session recording, auditing and protection for the applications powering your business.
To dig into more details and features, read today’s press release or browse the solution brief.























