
The idea of removing local administrator rights from Every. Single. User. across your organization is likely to spark strong reactions. Search popular online forums for the phrase “remove local admin rights” to see exactly what I mean. But hear me out …
Like most security professionals, you recognize the need – and urgency – to remove these powerful privileges from “regular” business users’ endpoints. Local admin rights are like carrots dangling out in the open, ready for cyberattackers to grab and use to move deeper into your network. Plus, typical workforce users don’t need total control of their systems, and they especially don’t need to run arbitrary code with elevated privileges. That’s far too risky.
But eliminating local admin rights completely? What about administrators and database administrators, the help desk, the infrastructure maintenance team and backup operators? They NEED high-level access to do their jobs, and your security team doesn’t have time or resources to manually grant extra privileges on the fly.
All this is true, but it doesn’t mean privileged users must be local admins. I’ll say it again: No user should be a local admin. Full stop. Here are 29 reminders why (and this is by no means an exhaustive list).
A user with local admin rights, or an attacker impersonating the user, can:
- Change boot and hardware configurations (enable/disable devices, change CPU and memory voltage and frequencies, etc.)
- Modify or delete storage volumes
- Radically simplify malware techniques, such as code injection and DLL hijacking
- Easily gain persistence on a machine with the registry fully open for analysis and modification
- Disable journaling, alter or wipe events
- Disable backup agents or modify backup configurations … and wipe any local backup copy while they’re at it
- Modify shadow copy settings or copy shadow copy (to exfiltrate previously “deleted” data)
- Modify users, add users, add administrative users or hide administrative users from the login menu
- Access every user’s data on the machine and change file and folder owners
- Encrypt hard drive master boot record (MBR), also known as a 15-second full-disk ransomware encryption
- Disable or reconfigure existing endpoint security solutions
- Change network settings, add trust zones, set up tunnels or reroute traffic
- Change the domain name system (DNS), hijack the DNS or exfiltrate data through DNS requests
- Modify browser settings or add browser extensions
- Access every secret stored on the machine: In Windows credential providers, in the browser, in Putty, in FileZilla or any other program that stores credentials
- Access and modify certificate stores, change trust chains and decrypt any secure communication
- Live off the land luxuriously
- Access, analyze and modify memory content
- Use security services to gain code execution in local security authority server service (LSASS), which can also be used to extract password hashes and Kerberos tickets
- Install ANY non-malicious administrative tool and deploy an arsenal of benign tools (that become the “ultimate attacker toolkit” in the wrong hands) without triggering the antivirus
- Install cryptominer malware to take over the machine’s resources and use them for illicit cryptocurrency mining
- Enable built-in or third-party hardware trackers to locate devices anywhere in the world
- Bypass and/or disable user access control (UAC)
- Downgrade drivers, versions and libraries, or force the use of known vulnerable protocols and programs
- Flash firmware to connected devices (e.g., disable LED on a camera or load modified firmware on to a PLC)
- Access security tokens and encryption keys
- Jump air gaps to access critical operational technology (OT) systems
- Access supervisory control and data acquisition (SCADA) control panels for critical infrastructure, then modify hardware parameters to disable safety sensors or cause hardware resonance
- And last but not least, choose their own adventure: Install, remove, access, read, exfiltrate, intercept, unpack, analyze, dump, encrypt, reconfigure, unload, load, enable, disable, execute or remotely execute, cause, force, flip, wipe, mess with and wreak havoc, while also hiding, concealing, dwelling, impersonating, watching, listening, spying, learning and preparing
TL; DR: Eliminate Local Admin Rights Across the Board
Didn’t read through all 29 (and counting) local admin superpowers? Here’s the bottom line: With full admin rights, even the most well-meaning, conscientious workforce user has too much control over your organization’s digital environment, putting critical data and systems (even your existing security stack) in jeopardy.
Not every action listed above requires admin rights, and some attacks will ultimately slip past some endpoint defense-in-depth layers. But assuming breach, eliminating local admin rights across the board and enforcing least privilege at the endpoint (and everywhere else) make it so much harder for attackers to achieve their goals that a majority will look elsewhere.
Removing local admin rights as a security measure is not going to be a revelation to you as a security pro, or to anybody even remotely associated with IT, for that matter. But if you’re anything like me, seeing so many risky possibilities in one place is helpful for making the step from understanding to action.
Now I know what you’re thinking. Restricting users to work under standard user accounts will have a profound positive impact on security, but if cutting admin privilege rights creates significant friction for users, your job will get even more difficult (not to mention the inevitable backlash from angry users).
Once bitten and twice shy, some IT folks even go as far as to say that removing local admin rights hurts an organization more than it helps it. And those who are not that radical probably had some different experiences based on their setup — maybe they just spend their day remoting into user machines to install a font or a printer, update a program or change the time zone. Or maybe they tried to force their way on to the users and eventually had to budge and give the local admin rights back.
All these challenges can be solved by a well-rounded endpoint privilege manager that can remove local admin rights and then, based on policies, elevate certain programs or tasks in a transparent manner so a user would never see a prompt or need to ask IT for assistance. And if they have some special case, users can request elevation, which can be approved without ever remoting to the machine. On the backend, an effective endpoint privilege manager would even integrate with an IT ticketing system for smooth workflows and fast elevations (helpdesk teams, rejoice!).
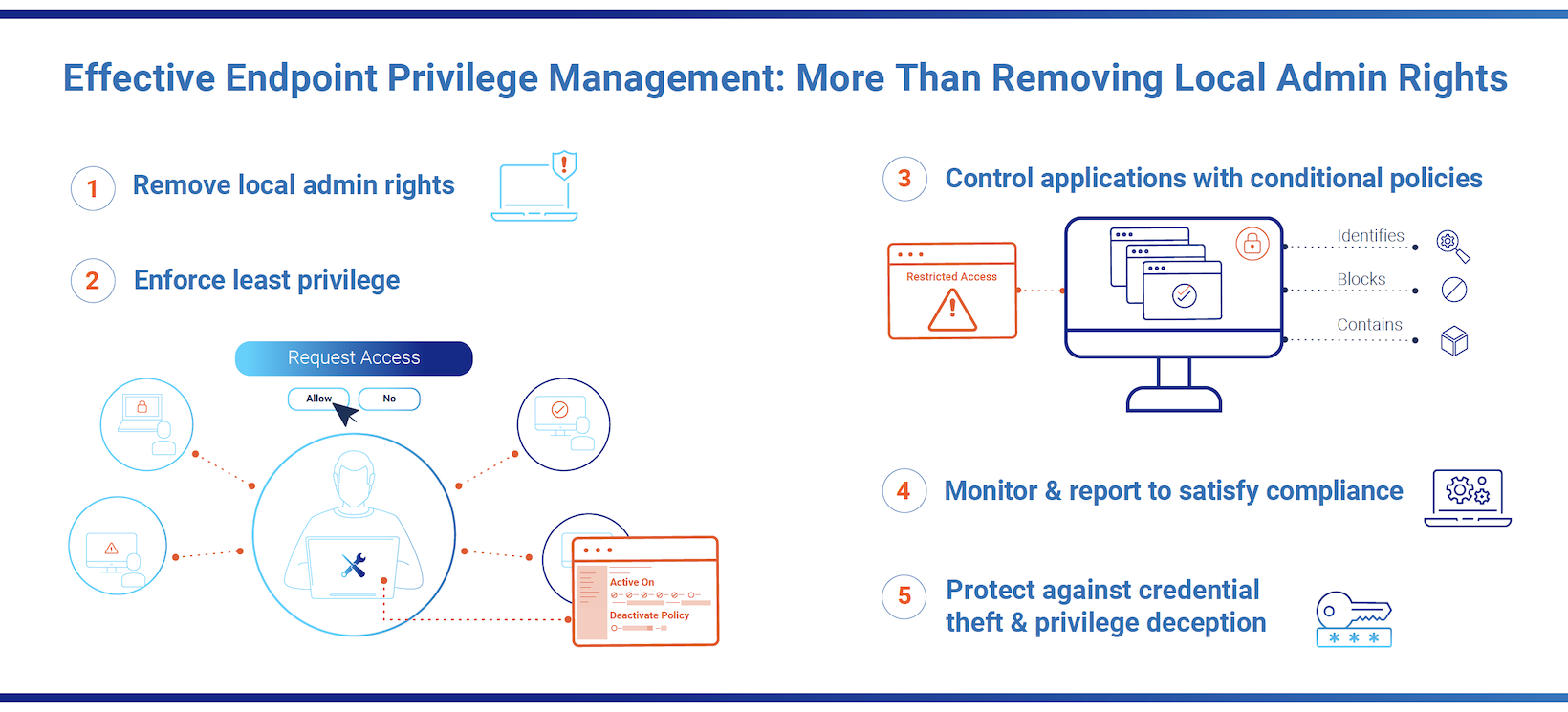
Endpoint privilege managers are the cornerstone of the modern endpoint security stack, but not all solutions are created equal. A best-of-breed endpoint privilege manager will enable your organization to:
- Remove local admin rights and enforce least privilege to reduce endpoint security vulnerabilities, then elevate end-user privileges on demand, in real time, with little or no helpdesk involvement.
- Block ransomware by tightly controlling application permissions based on fine-grained, conditional business rules. Defend against other threats targeting and originating on endpoints.
- Protect against credential theft by safeguarding credential stores, helping to contain attackers and reduce the attack blast radius.
- Enhance the user experience by giving the right people and applications the right access to the right resources at the right times.
- Satisfy audit and compliance requirements by making it easy to enforce and demonstrate policies.
- Protect Windows, Windows Server, MacOS and Linux endpoints from hybrid to cloud environments, while extracting value from day one and realizing rapid ROI.
Need some more convincing that now is the time to remove local admin rights across your business? Explore this guide for key considerations and see how CyberArk Endpoint Privilege Manager can help your team strengthen endpoint security without complicating IT operations or impairing the user experience.




















