Some of the world’s most technologically advanced enterprises have grappled with identity-related breaches in recent months. These incidents have further highlighted how digital identities have come to simultaneously represent today’s greatest cybersecurity challenge and the core of modern enterprise security.
It’s become clear that a holistic, all-hands-on-deck approach is required to stay ahead of attackers and make it more difficult for them to succeed.
We recently explored key steps for mitigating risk if your Identity Provider (IdP) is compromised. Today’s post will take this a step further, illustrating four specific ways in which a security-first, defense in depth strategy can help organizations better protect their data, users and customers by layering Identity Security controls over baseline IdP deployments — no matter which platform or various integrated technologies are in play.
Use Case #1. Protecting endpoints and enforcing the principle of least privilege

A defense-in-depth approach promotes strong multi-factor authentication (MFA) at the endpoint — beginning with the login process, which should require two separate authentication methods for entry, such as a password and a one-time-password (OTP).
Ideally, user accounts should not have local admin rights, making tasks such as changing system configurations, installing software or changing account settings off limits. When a user requires elevated privileges to execute an administrative action or launch a sensitive application, they should be prompted by MFA to validate their identity again before being granted just-in-time access to the resources they need, for just the right amount of time.
Enforcing context-aware, risk-based MFA and least privilege on the endpoint helps to prevent attackers from gaining a foothold within an organization, launching ransomware and other user-based attacks and jump-starting a cascade of reconnaissance activities and lateral movement.
Use Case #2. Monitoring and auditing high-risk web application sessions
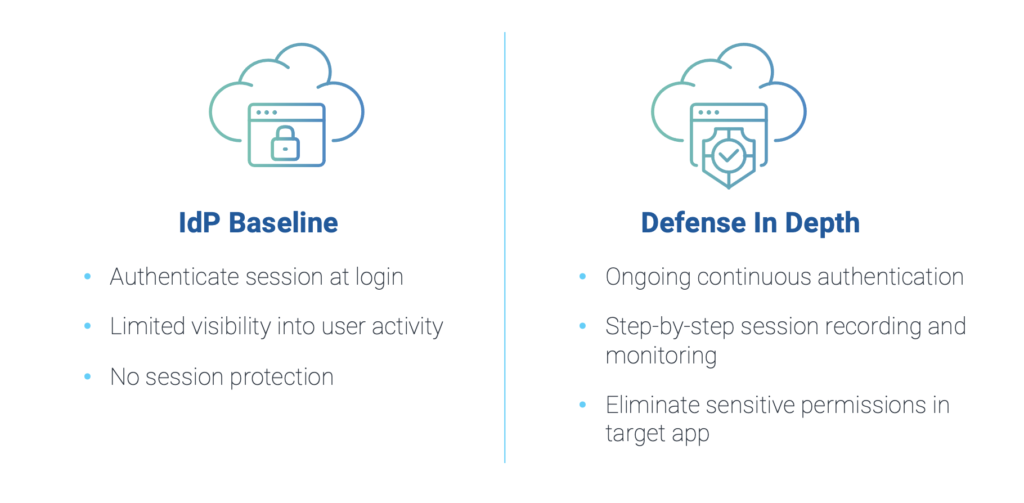
Nearly 80% of organizations report employee misuse or abuse of access to business applications. As more high-value data migrates to the cloud, a defense-in-depth approach is critical for managing web-application risk.
This starts by extending existing Single Sign-On capabilities to validate users at the beginning and during each session and enforcing global time-outs to minimize risk, such as when a user steps away from a device during a session. Implementing step-by-step session recording and monitoring within protected applications allows organizations to easily search for and audit actions — without impacting the user experience. To further protect sensitive data residing in applications, organizations can also choose to restrict data exfiltration actions, such as copying data and downloading files, and further limit individual user or application permissions based on specific needs and requirements.
Use Case #3. Storing and sharing credentials for password-based business apps and other sensitive data
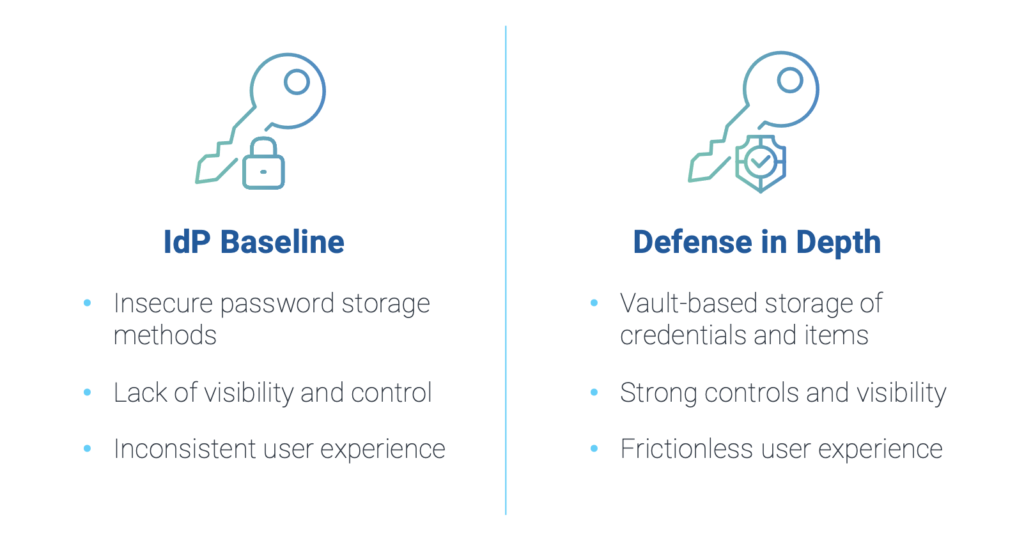
According to The CyberArk 2022 Identity Security Threat Landscape Report, credential access is the No. 1 area of risk for organizations today. Credentials are universally sought after as a means to compromise identities and launch attacks. Despite the widely known risks, business users are often left to manage credentials on their own — a major hassle that results in weak or reused passwords, credentials stored in plain text files, Excel spreadsheets or browsers, or the use of disparate password managers that limit security’s visibility and control.
A defense-in-depth approach can help eliminate password pains for business apps and other sensitive data, while boosting the overall user experience. By deploying a centralized vault-based storage system and making it accessible via passwordless authentication, an employee can simply login using an MFA QR code, for example, and then seamlessly add passwords, license numbers, encryption keys and other valuable data to the vault, securely accessing and sharing them with other users with a click of a button.
Use Case #4. Providing secure third-party privileged access to critical internal resources
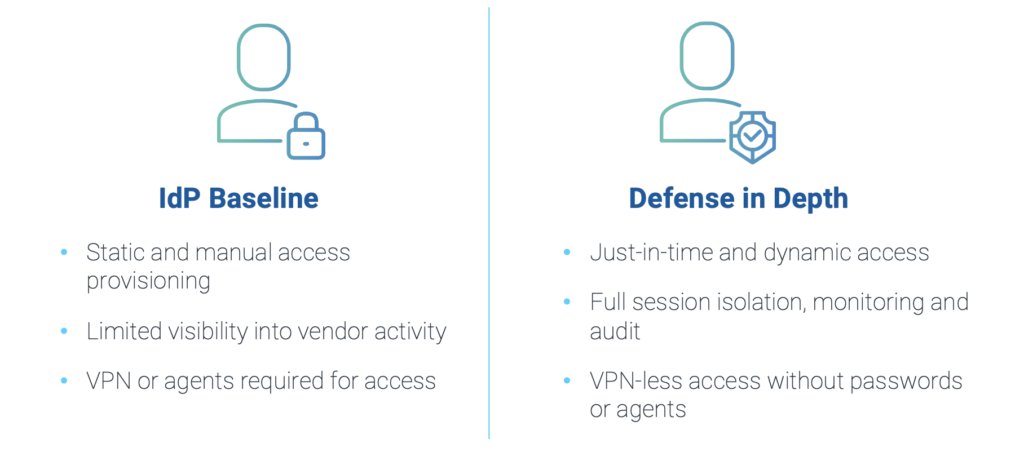
More than 96% of organizations allow third-party access to critical systems today. To perform their intended tasks, these authorized third parties require rapid and secure provisioning/de-provisioning of privileged access to specific corporate IT systems. The challenge for organizations is to do so efficiently, securely and in compliance with a growing body of regulations.
Third-party policies must mirror established Zero Trust policies for internal employees, such as authenticating each time they require access. An effective defense-in-depth approach will allow vendors to bring their own decentralized identity to gain access to privileged resources via a universal portal — enabling simple yet secure authentication and providing vendor managers the ability to manage their own users’ access.
To improve security posture and reduce complexity, dynamic, just-in-time provisioning to privileged accounts can be granted on the fly for specific reasons and for specific amounts of time. Doing so without the need for passwords, tokens and network-based access controls further reduces the attack surface. And by enabling full session isolation, real-time monitoring and audit, organizations can increase their visibility into vendor activity — critical for reducing supply chain risks.
Close IdP Gaps with a Security-First, Defense-in-Depth Approach
No matter your organization’s industry or size, security matters. Take the time to evaluate your digital identity landscape for potential gaps and learn how a defense in depth approach can help address security vulnerabilities and provide additional assurances. Then, with a clear understanding of where you are today, prioritize Identity Security controls to help your organization get to where you want to be.
Explore lessons we can all learn from incidents targeting a critical security layer. And for more details on deploying CyberArk solutions alongside your current IdP to cover your Identity Security bases, tune in to the on-demand webinar “How to Leverage Defense in Depth to Minimize Risk.”























