
A new and concerning chapter has unfolded in these troubled times of geopolitical chaos. The Cozy Bear threat actor has caused significant breaches targeting Microsoft and HPE, and more are likely to come. These recent events have sent shockwaves throughout the tech community, and for good reason. As we continue to uncover the fallout from these breaches, it has become apparent that the magnitude of the incident is more significant than we first realized. Today’s blog post sheds light on who exactly APT29 is, its motives, what tactics it continues to use – and ultimately, how organizations might prevent similar attacks from happening to them.
Who’s Behind the Microsoft Attack and Why?
The U.S. government has classified this threat actor as the advanced persistent threat APT29. The group also goes by many other names, such as CozyCar, The Dukes, CozyDuke, Midnight Blizzard (as Microsoft calls them), Dark Halo, NOBELIUM and UNC2452. Most people, however, know it by the moniker Cozy Bear. This group has rightfully earned a reputation as one of the world’s most advanced and elusive espionage groups.
In reviewing security camera footage, the Dutch government determined that the Russian Foreign Intelligence Service (or SVR) led this group. APT29’s primary objectives include acquiring political, economic and military intelligence to gain a competitive advantage, supporting geopolitical goals and enhancing Russia’s influence on the global stage. The group’s long-term and covert approach reflects its commitment to achieving sustained access to sensitive information, allowing it to conduct strategic operations over an extended period.
Industry experts generally agree that this threat actor formed in 2008 and has been targeting government entities, think tanks and critical infrastructure since 2010. Cozy Bear has since been linked to several high-profile cyber-attacks, including the 2016 breach of the Democratic National Committee (DNC), the SolarWinds supply chain attack of 2019 and the Republican National Committee (RNC) in 2021. This threat actor is known to be extremely patient and cautious. Cozy Bear sometimes dwells inside a network for years if the target is valuable enough.
Quick aside: An interesting thing to note is that the SolarWinds breach was the first time an attack method called Golden SAML was documented in the wild. The attack method was first discovered by CyberArk Labs’ Shaked Reiner in 2017.
What Happened to Microsoft (What We Know So Far)
On Jan. 12, Microsoft detected a threat actor who gained access to a small percentage of corporate email accounts, exfiltrated emails and attached documents of high-value targets, including those of senior leadership, cybersecurity and legal teams, along with other internal employee identities.
Based on the details provided by Microsoft at the time of this writing, it appears the initial objective of the attack was to acquire information. Once inside target email accounts, Cozy Bear searched for specific information about, well, Cozy Bear. The group likely wanted to better understand its adversary (the intelligence teams gathering information on it) and discover the countermeasures intended to lure and stop it. Examples of what the threat actor might be interested in include indicators of compromise (IoC), exposed cloud infrastructure used by the attacker, IP ranges and known tactics, techniques and procedures (TTPs).
Analyzing the Microsoft Breach
Based on the information provided by Microsoft on Jan. 19, it appears the threat actor gained access to a “legacy, non-production test tenant account” through a password spray attack.
Password spraying is a brute-force attack where the attacker slowly tries a list of passwords against accounts from various source IP addresses. This simple attack keeps the number of requests below the standard rate limit to stop rapid login attempts from single IP addresses. This technique helps its attacker avoid detection by not locking out user accounts due to multiple failed login attempts, a common identity threat detection and response (ITDR) capability offered in access management and privileged access management (PAM) solutions. This type of attack is significantly slower but much more difficult to detect. Subsequently, password spraying has a much higher chance of succeeding.
Using this technique, the attacker compromised and accessed the account. The question that comes to mind is, if this was publicly facing, why was multi-factor authentication (MFA) not part of the authentication flow?
In this situation, the permissions set was limited. However, the test account had access to an OAuth application that had elevated access into their corporate environment. Although this was deemed a “legacy” account, it still was authorized to access the production systems. This coverage gap is a familiar blind spot for many organizations; even with great technical controls to implement least privilege access, people and processes (such as ongoing entitlement reviews) remain essential elements of identity security programs.
At this point, the attacker created a series of malicious OAuth applications that enabled them to have multiple hooks into the target, providing higher persistence while making the defender’s job even harder. Afterward, the threat actor created a new user account to grant access to the Microsoft corporate environment for the other newly created and malicious OAuth applications. Then, the attacker used the initial compromised legacy test OAuth application to grant the newly created OAuth apps the Office 365 Exchange Online *full_access_as_app* role. This role typically grants extensive access and privileges to an application – which, in this case, allowed access to target mailboxes.
The granted privilege here is meaningful because it enabled the adversary to read and exfiltrate emails and attachments. This unauthorized connection was accomplished by generating valid access tokens to Microsoft’s Exchange server, even if the original user was not allowed to do so.
Surmised Microsoft Attack Flow
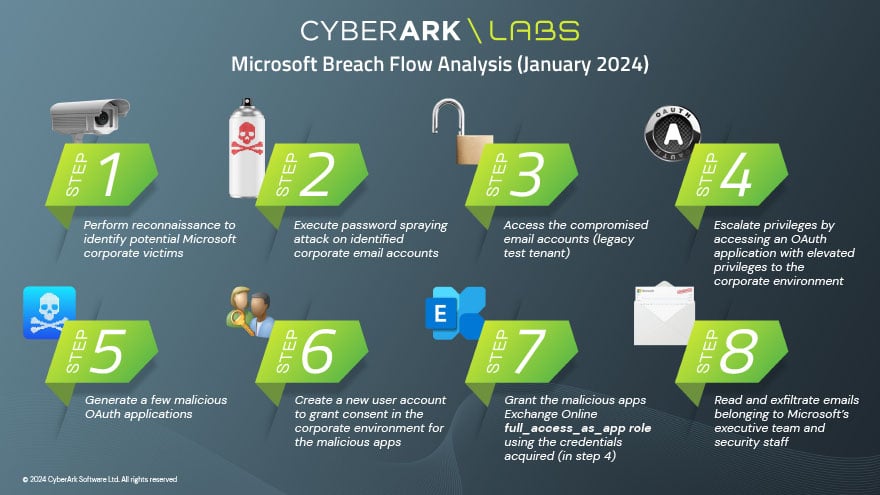
The graphic above charts APT29’s steps:
- Performed reconnaissance to identify potential victims (e.g., through LinkedIn, OSINT).
- Performed password spraying attack on the identified entities discovered in step 1.
- Accessed the compromised account (legacy test tenant).
- Escalated privileges by accessing an OAuth application with elevated privileges to the corporate environment.
- Created a few malicious OAuth applications.
- Created a new user account to grant consent in the Microsoft corporate environment for the malicious apps created in step 5.
- Granted the malicious apps Office 365 Exchange Online *full_access_as_app* role using the credentials gained from step 4.
- Read and exfiltrated emails belonging to Microsoft’s executive leadership team and security staff.
Prerequisite Misconfiguration Assumptions
Based on the information disclosed, we assume that certain misconfigurations were present:
- Access to an OAuth application with elevated permissions to the internal environment.
- Privileges allowing the creation of OAuth apps and users.
- Privileges for reading emails.
It’s also worth mentioning that even though this attack created limited practical impact (stolen emails and file attachments), it can still escalate damage through various other paths, such as the exfiltration of regulated data or the disruption of systems.
What Your Organization Can Do to Help Prevent a Similar Attack
Protect Your Non-production Environments
One common mistake IT organizations make is that under-protected development environments are exposed to the internet, allowing access to threat actors. These environments should be segmented and not easily accessible from outside an organization’s perimeter. Organizations should extend cybersecurity controls in production environments into non-production environments – failure to follow best practices cause data breaches.
Another common mistake I see organizations make is using unsensitized data in test environments, allowing easy exfiltration. End user emails and attachments were not present in the legacy tenant. Still, Microsoft admitted it used the same credentials in its production environment and this legacy tenant. The threat actor’s ability to pivot and access production data resulted from reusing privileged credentials and the absence of segmenting nonproduction and production environments.
Because organizations cannot implicitly trust that best practices are adhered to by the people implementing the environments, we need to extend multiple controls, such as MFA, to environments outside of production. Everyone knows that MFA is important. That said, many organizations, including one of the largest tech giants in the world, didn’t use it correctly, at least in this case. Additionally, we must assume that systems are not always set up securely. Misconfigurations and accounts being over-provisioned are inevitable, which is why we preach taking a defense-in-depth approach to cybersecurity. Leveraging controls like least privilege and MFA to non-production environments is incredibly important.
Implement Identity Threat Detection and Response (ITDR)
The ATP29 attack on Microsoft is a textbook example of how ITDR is critical to an organization.
Starting with the initial access through password spray using a proxy, the lack of MFA followed – and the creation of privileged OAuth applications eventually led to generating a user account with a sensitive privilege … All these actions had the potential for detection and response.
Like every element of cybersecurity, ITDR capabilities are more effective when tightly integrated into an identity fabric that proactively reduces risk rather than waiting for an attack to be detected. CyberArk Labs is working on a project in the ITDR world, and we are pleased to share that our suggested ITDR list of rules covers most aspects of the attack.
Defenders should re-evaluate the effectiveness of their password spray detections against the “low volume” style of attack described above. The focus on OAuth emphasizes the importance of such detections and the need for a comprehensive ITDR solution covering both on-prem and Cloud aspects.
An additional line of defense includes having controls to prevent credentials reuse and to rotate all credentials consistently according to organizational policy. Finally, detecting the entry of risky commands could have further reduced the risk of this attack by limiting lateral and vertical movement.
Security teams should carefully review every impersonation action between non-human and human entities. Require administrative privileges for the OAuth application approval process (Consent).
Suggested ITDR Detections and Responses
The following recommendations correspond to password spraying attacks, OAuth abuse, and other malicious actions. You can monitor the following events to detect:
- Login without MFA (and respond automatically, accordingly)
- Reuse of authentication credentials and force rotation
- Suspicious creation or reactivation of OAuth applications
- The idle activity of an OAuth application
- New admin privileges granted to a user and try to add correlation with deviation from an approved organizational process for changing and adding privileges (e.g., the need to open an IT support ticket or to authenticate with MFA again)
- The activity of a user without a prior explicit user authentication (or session start event)
- MFA-configured user behavior without a prior MFA check
- Attempted actions that failed due to the post-expiration time of the credentials\tokens\cookie used
- Entry of malicious commands
- Attempts to bypass privileged access management solutions
- User login using a proxy
The Time to Act is Now (and Always)
This recent attack on Microsoft is a stark reminder of the persistent and sophisticated threats from nation-state threat actors. And it isn’t likely the last we’ll see from Cozy Bear. Days after Microsoft’s breach announcement, other organizations have also announced they had fallen victim to this threat actor. CyberArk Labs expects that more attacks will continue to become public now that these indicators of compromise are available to everyone. It’s also essential to acknowledge that the threat landscape is not limited to a single actor or nation. Other states are actively developing and refining their cyber capabilities, ready to launch similar attacks with varying motives.
The attack is also a sobering glimpse into the future of cyber warfare. It serves as a call to action for heightened vigilance, collaboration and investment in cybersecurity. The looming specter of nation-state cyberattacks demands our attention, and the time to fortify ourselves is now. Ignoring these warnings would be to our peril. As a global community, we must work collectively to safeguard our digital infrastructure from the growing threat of nation-state cyber aggression.
Andy Thompson is CyberArk Labs’ Offensive Security Research Evangelist.
Editor’s note: For more insights from CyberArk Labs’ Andy Thompson on this subject and beyond, check out his appearance on CyberArk’s Trust Issues podcast episode, “Behind the Data Breach: Dissecting Cozy Bear’s Microsoft Attack.” The episode is available in the player below and on most major podcast platforms.























