Endpoint security is the practice of protecting enterprise networks against threats originating from on-premises or remote devices. An endpoint is any device that provides an entry point to corporate assets and applications and represents a potential cybersecurity vulnerability. Examples include desktops, laptops, servers, workstations, smartphones and tablets.
Historically, most organizations have used conventional security products like firewalls, VPNs, endpoint management solutions, and antivirus programs to safeguard sensitive information, prevent unauthorized access to critical applications and IT systems and protect against malicious software and other vulnerabilities. But, businesses are increasingly adopting mobile applications and cloud services, eroding the once well-defined enterprise network perimeter. Cyber attackers are becoming more and more sophisticated and are increasingly able to evade traditional security measures. Many enterprises are now taking a defense-in-depth approach to endpoint protection, instituting a wider range of security controls to protect against a broader array of threats.
A Defense-in-Depth Approach to Endpoint Security
Originally conceived by the U.S. National Security Agency, a defense-in-depth approach employs multiple layers of security to eliminate gaps, reduce attack surfaces and contain threats.
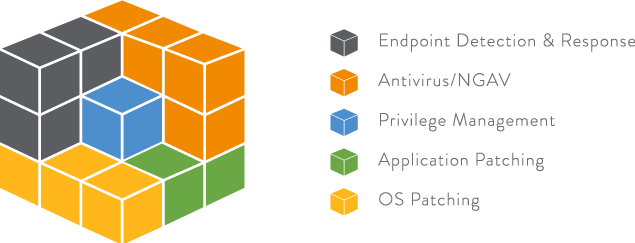
A complete defense-in-depth endpoint security strategy includes five key endpoint security and management measures:
- Endpoint detection and response (EDR) tools to proactively identify and investigate suspicious activity on endpoint devices. Most EDR solutions continuously monitor, record and analyze endpoint events, helping IT and security professionals efficiently detect and mitigate advanced threats.
- Antivirus and next-generation antivirus protection solutions to prevent, detect and remove various forms of malware. Traditional antivirus programs use signature and heuristic techniques to identify and remove unwanted programs. Next-generation antivirus protection (NGAV) solutions use analytics and machine learning to defend against cutting-edge attacks such as ransomware and advanced phishing that can elude conventional antivirus programs.
- Operating system patching to mitigate common vulnerabilities and exposure (CVE). All leading operating system vendors routinely issue software updates to address known security issues. Enterprise IT and security organizations can reduce risk by instituting automatic O.S. updates and implementing other systems and practices to ensure all corporate PCs, servers and mobile devices are running the latest operating system releases.
- Application patching to eliminate security risks associated with individual software applications. Organizations can improve their security posture by ensuring all enterprise desktop, server and mobile apps are up-to-date. According to one study, 90% of production applications use a library with a known CVE.
- Privilege management to grant users and processes the bare minimum set of entitlements they need to perform their required tasks. Also known as the principle of least privilege (POLP), privilege management removes local admin rights on servers and personal computers, restricting access privileges to authorized users and applications to reduce risk.
Benefits of an Endpoint Privilege Management Solution
Endpoint privilege management solutions help strengthen security and reduce risk by eliminating unnecessary local administrator privileges from endpoint devices and by containing malicious applications and other threats at the endpoint. A fundamental component of a defense-in-depth endpoint security strategy, an endpoint privilege management solution provides a critical layer of protection when an attack evades traditional perimeter and endpoint security controls.
Endpoint privilege management solutions let enterprise IT operations, security and compliance teams:
- Institute least privilege access for endpoint devices, bolstering security.
- Secure and rotate local administrator passwords, preventing credential theft.
- Prevent end-users from installing unsanctioned applications, reducing exposure.
- Run unknown applications in a restricted mode, preventing access to corporate assets or confidential data.
- Protect against, block and contain malicious programs and attacks on the endpoint, preventing lateral movement and malware spread, reducing risk.
- Implement endpoint security policies to ensure compliance with corporate guidelines or government regulations.
- Automatically elevate privileges based on policies, improving user productivity, while reducing the IT burden.